The recent exploit of the Kelp liquid restaking protocol, resulting in a loss of approximately $293 million, has starkly underscored the inherent dangers of non-isolated lending and deeply integrated functionalities within decentralized finance (DeFi). This incident, according to leading crypto industry executives and blockchain security firms, serves as a critical illustration of how vulnerabilities in one protocol can rapidly cascade, triggering broader ecosystem contagion and posing systemic risks across the interconnected DeFi landscape.
The Exploit: A Catalyst for Contagion
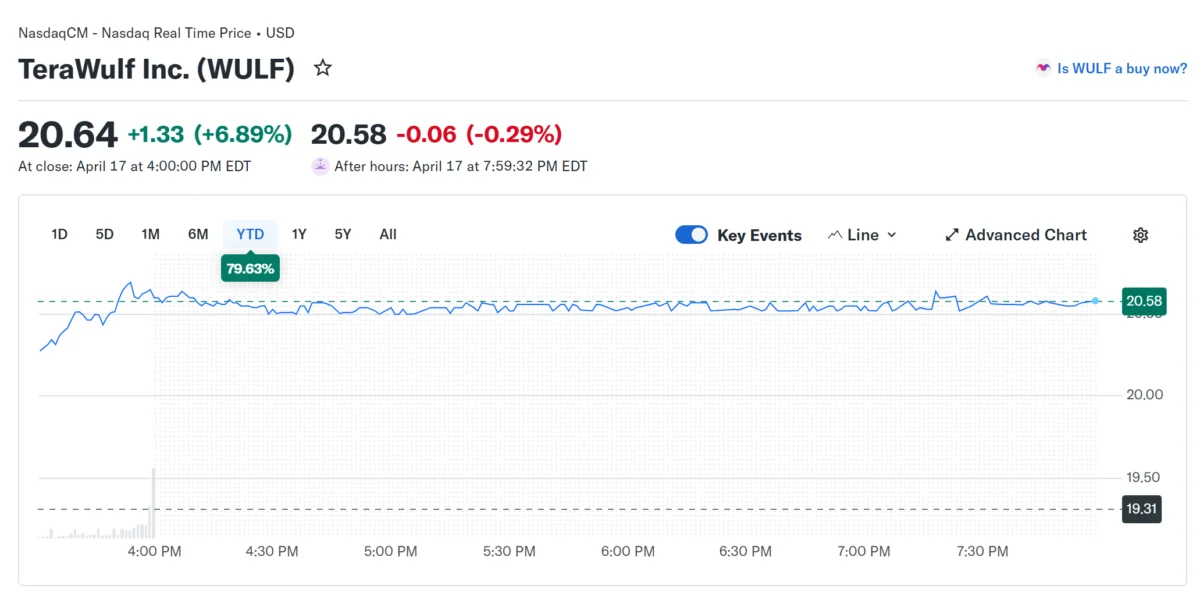
On Saturday, the Kelp liquid restaking platform fell victim to a sophisticated cyber attack that led to the draining of a significant sum, estimated at $293 million. In the immediate aftermath, Kelp moved to pause smart contracts associated with its restaking token, rsETH, while launching an urgent investigation into the breach. This incident was not merely an isolated attack on a single protocol; it swiftly evolved into a cross-protocol contagion event, sending ripples through multiple integrated DeFi platforms.
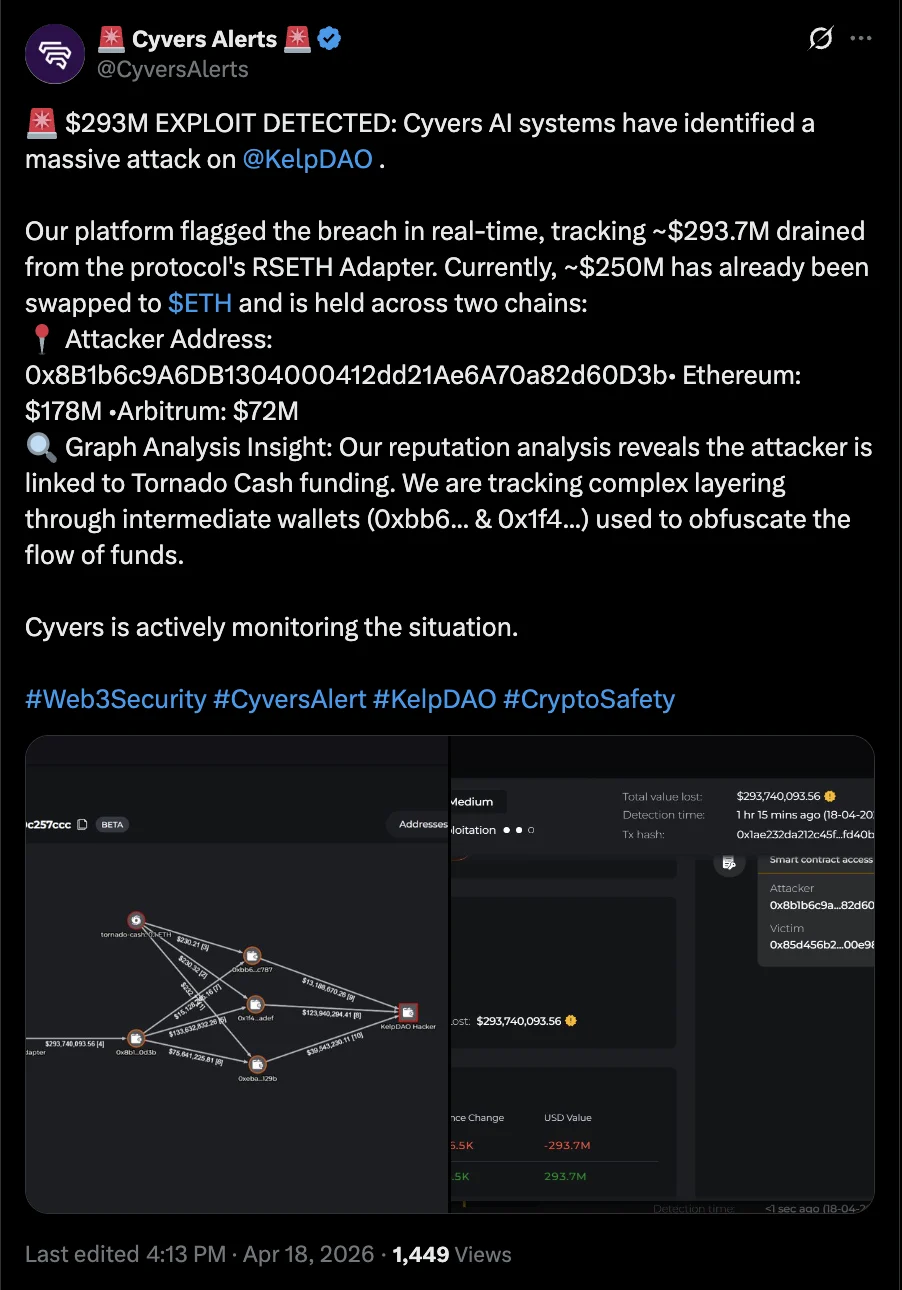
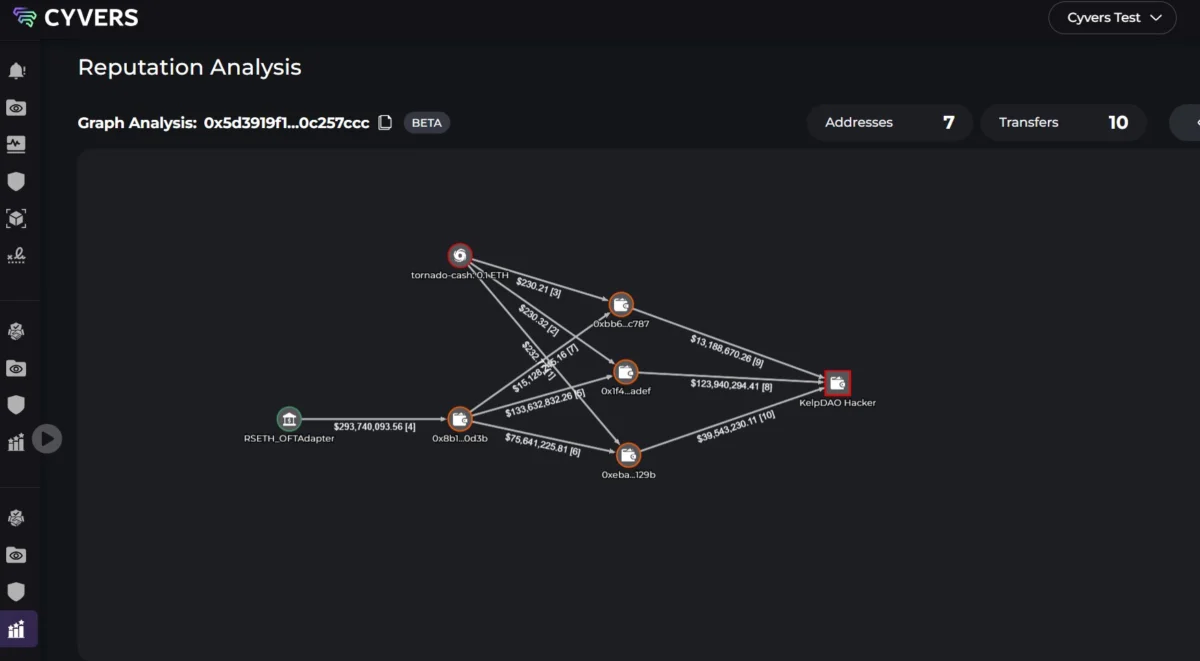
Blockchain security firm Cyvers confirmed the extensive reach of the exploit, reporting that at least nine prominent DeFi protocols and platforms were directly affected. Among those compelled to take swift action were major players such as Aave, Fluid, Compound Finance, SparkLend, and Euler. These platforms, which had exposure to rsETH markets, moved to freeze affected markets or implement other mitigation strategies to contain potential fallout and protect their users from further losses. Deddy Lavid, CEO of Cyvers, articulated the evolving challenge facing the industry: "The challenge is no longer just preventing exploits at the contract level, but understanding how fast they can cascade across integrated protocols." This statement highlights a paradigm shift in blockchain security, moving beyond individual smart contract audits to a more holistic view of systemic risk management.
Root Causes: Non-Isolated Lending and Cross-Chain Vulnerabilities
The exploit on Kelp has brought into sharp focus two primary architectural risks within DeFi: non-isolated lending and the complexities of cross-chain bridging. Michael Egorov, the founder of the pioneering Curve Finance DeFi protocol, has been a vocal proponent of caution regarding these intertwined elements. He explained that non-isolated lending on DeFi platforms, reminiscent of earlier iterations of protocols like Aave, inherently exposes users to risks stemming from all the diverse tokens utilized as collateral. In such a setup, a vulnerability or significant price fluctuation in one collateral asset can imperil the entire lending pool, affecting users who may have collateralized with entirely different, otherwise stable assets.

Egorov further emphasized the critical importance of rigorous due diligence by DeFi teams. He stressed the necessity of thoroughly vetting prospective digital assets to ensure they do not possess single points of failure or exploitable attack surfaces before being approved as lending collateral. This proactive approach is vital in preventing compromised tokens from infiltrating and destabilizing otherwise robust lending ecosystems.
Beyond lending mechanics, the Kelp exploit also highlighted the perils associated with cross-chain bridging architecture. Egorov pointed to the transfer of assets from one blockchain protocol to another via cross-chain bridges as a root cause of this particular weekend’s exploit. "Cross-chain is hard and potentially risky," Egorov cautioned. "Only use cross-chain infrastructure when absolutely necessary, and do it really carefully." This admonition underscores the intricate technical challenges and expanded attack vectors introduced by interoperability solutions, which, while offering greater liquidity and user experience, simultaneously create complex security dependencies.
The Rise of Liquid Restaking and its Associated Risks
To fully comprehend the significance of the Kelp exploit, it is crucial to understand the context of liquid restaking within the broader DeFi landscape. Liquid restaking protocols, often built atop foundational protocols like EigenLayer, allow users to "restake" their already staked Ether (ETH) or other assets, receiving a liquid staking token (LST) or liquid restaking token (LRT) in return, such as Kelp’s rsETH. This process enables users to earn additional yield on their staked assets by participating in multiple security layers simultaneously, effectively compounding their rewards.
The innovation of liquid restaking has been a major narrative in DeFi, attracting substantial capital and fostering rapid growth. However, this innovation also introduces layers of complexity and interconnectedness. When rsETH, a derivative of restaked ETH, is then used as collateral in lending protocols, it creates a dependency chain. A vulnerability in the underlying restaking protocol (Kelp) or a flaw in the rsETH token’s smart contract can directly impact the stability of all protocols that accept it as collateral. This amplified interconnectedness, while efficient for capital utilization, also creates fertile ground for systemic risk propagation, as witnessed in the Kelp incident. The promise of higher yields often comes with a commensurate increase in risk, and the Kelp exploit serves as a powerful reminder of this fundamental principle.
A Broader Trend of Escalating Crypto Hacks
The Kelp exploit is not an isolated incident but rather a stark indicator of a troubling trend in the Web3 space. The first quarter of 2026 alone saw losses from crypto hacks, code exploits, and scams reach an alarming $482 million. This figure highlights a persistent and escalating threat landscape that continues to plague the nascent industry.

Just last week, the Drift Protocol decentralized exchange suffered a $280 million hack, preceding the Kelp incident. Furthermore, the early part of this month witnessed at least 12 other crypto platforms and DeFi protocols falling victim to various attacks. These events collectively paint a picture of an industry grappling with sophisticated adversaries and the inherent security challenges of rapidly evolving, open-source financial infrastructure. From domain hijacking incidents, such as the one affecting the DAO behind CoW Swap, to complex smart contract exploits, the methods of attack are diverse and constantly evolving. This relentless barrage of security breaches underscores the urgent need for heightened security measures, continuous auditing, and robust risk management frameworks across the entire DeFi ecosystem.
Lessons Learned and the Path Forward
The Kelp incident, while damaging, is being framed by industry experts as a critical learning experience for the DeFi sector. Michael Egorov highlighted this perspective, stating that the sector can leverage such incidents to grow, mature, and implement more robust cybersecurity protections. This sentiment resonates across the industry, with a collective understanding that security must remain paramount, even amidst rapid innovation.
The implications of the Kelp exploit extend far beyond the immediate financial losses. They touch upon several critical areas:
- Systemic Risk: The "cross-protocol contagion event" clearly demonstrates how DeFi’s composability, while a strength, can also be a major vulnerability. The interconnectedness of protocols means that a failure in one can quickly propagate, posing systemic risks to the entire ecosystem. This necessitates a re-evaluation of how inter-protocol dependencies are managed and stress-tested.
- Trust and Confidence: Repeated high-profile exploits erode user and institutional trust, which is fundamental for the mainstream adoption of DeFi. Rebuilding and maintaining this trust requires a transparent and proactive approach to security, including rapid response mechanisms and clear communication during incidents.
- Security Audits and Due Diligence: The incident reinforces the need for exhaustive security audits, not just of individual smart contracts but also of the entire integrated system, including third-party dependencies and cross-chain interactions. DeFi teams must go beyond basic audits and implement continuous security monitoring, bug bounty programs, and real-time threat intelligence.
- Risk Management Frameworks: Protocols must develop more sophisticated risk management frameworks that account for the composable nature of DeFi. This includes establishing clear parameters for collateral types, implementing circuit breakers, and having contingency plans for rapid response to unforeseen events.
- Education and User Awareness: Users must also be educated about the risks associated with various DeFi activities, particularly those involving complex derivative tokens and cross-chain transfers. Understanding the potential for impermanent loss, smart contract risk, and systemic contagion is crucial for making informed decisions.
- Potential Regulatory Scrutiny: A continued pattern of significant exploits and contagion events could attract increased attention from regulators globally. While DeFi prides itself on decentralization, a lack of self-governance and robust security could lead to external intervention, potentially stifling innovation.
In response to these challenges, the DeFi community is increasingly mobilizing efforts, such as the formation of "white hat" teams like "SEAL 911," which aim to fight crypto hacks in real-time. These collaborative initiatives signify a growing recognition that collective security is paramount.
The Kelp protocol exploit serves as a sobering reminder that while DeFi offers unprecedented opportunities for financial innovation, it also presents complex and evolving security challenges. The path forward demands a commitment to continuous learning, rigorous security practices, and a collaborative effort across the ecosystem to build more resilient and trustworthy decentralized financial infrastructure. The industry’s ability to learn from these incidents and implement more robust safeguards will be critical for its long-term viability and widespread adoption.