Kelp, a prominent liquid restaking protocol, became the latest high-profile victim of a sophisticated cyber attack on Saturday, leading to an immediate halt in smart contract operations for its restaking token, rsETH. The platform initiated an urgent investigation into the breach amid initial reports suggesting losses potentially reaching hundreds of millions of dollars. The incident sends fresh ripples of concern throughout the decentralized finance (DeFi) ecosystem, highlighting persistent vulnerabilities in interconnected protocols and the escalating sophistication of crypto-related cybercrime.
The Anatomy of the Attack: Exploit of the rsETH Adapter Bridge
The attack unfolded rapidly, with Kelp DAO first identifying "suspicious cross-chain activity involving rsETH" early on Saturday. In response, the protocol promptly announced via an X (formerly Twitter) post that it had "paused rsETH contracts across mainnet and several Layer-2s" to mitigate further damage and investigate the root cause.
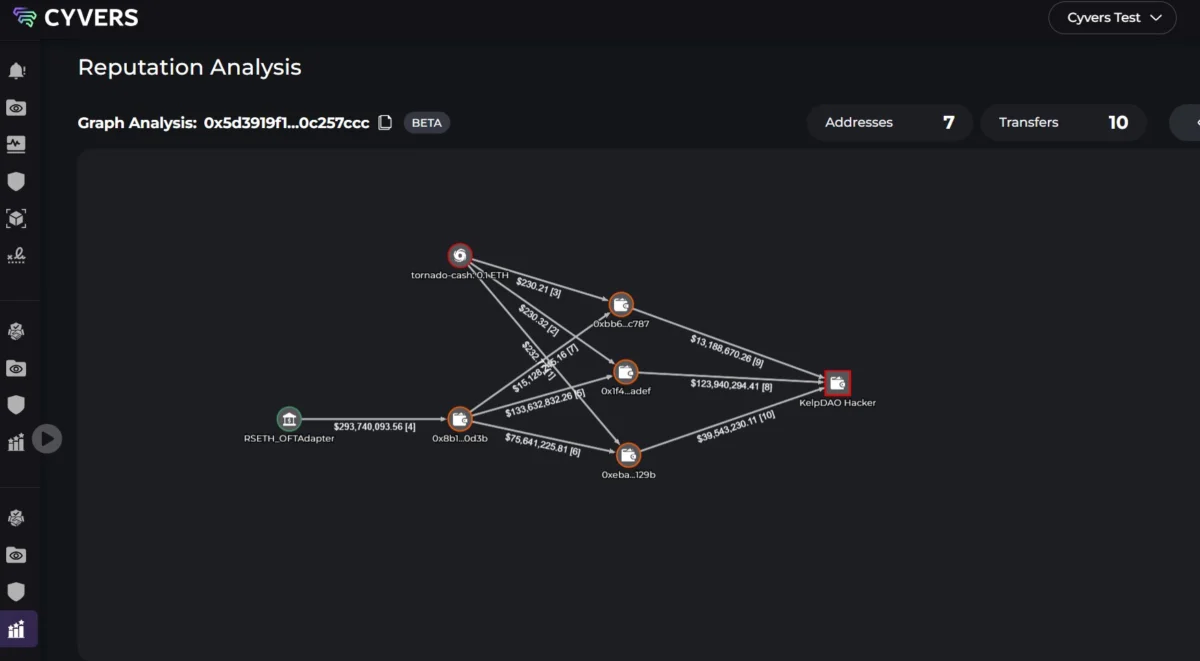
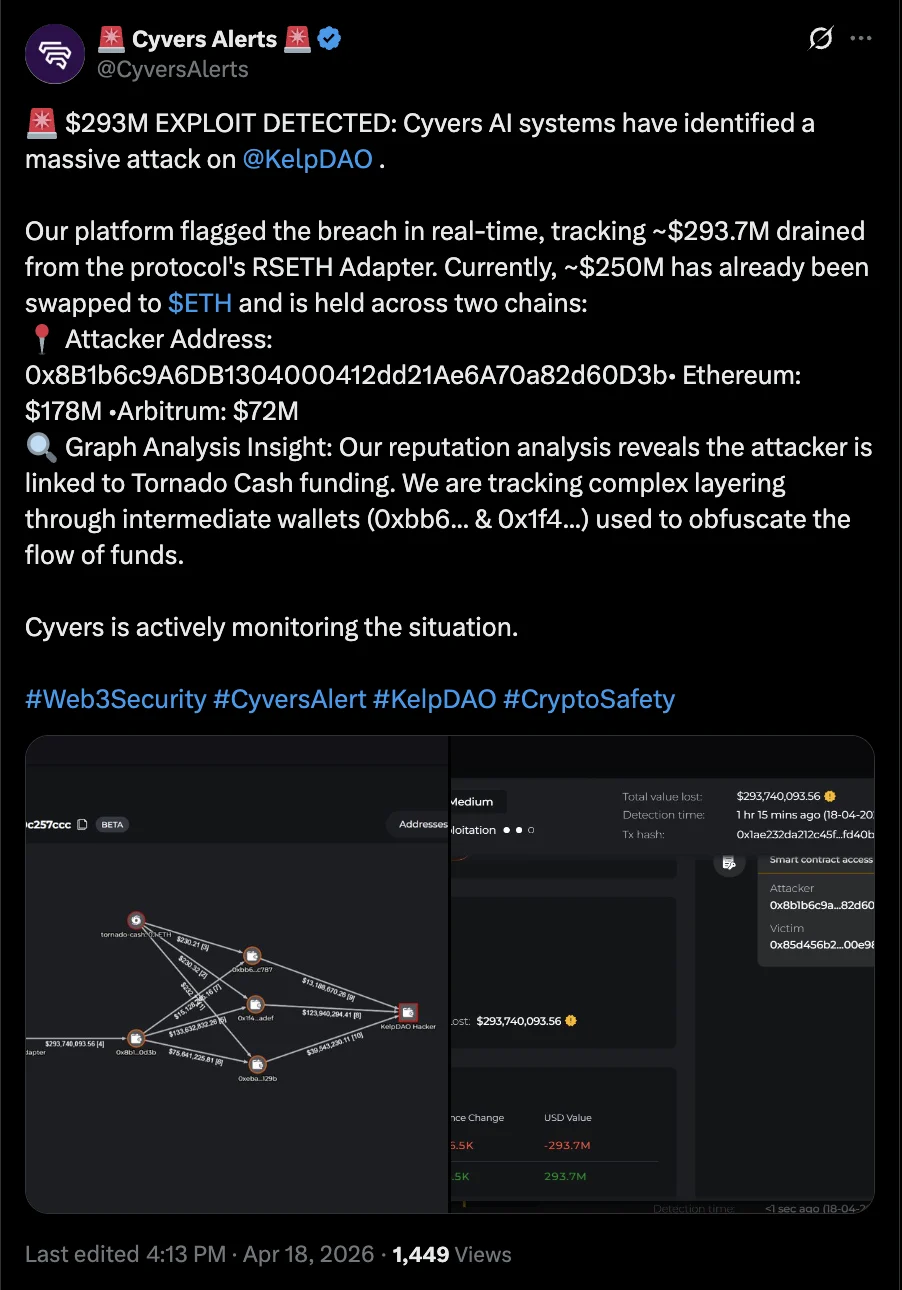
Subsequent analysis by blockchain security firm Cyvers revealed the specific vector of the attack: an exploit targeting the rsETH adapter bridge contract. This critical piece of software code is responsible for managing and facilitating the movement of Kelp’s rsETH token across different blockchain networks. Attackers successfully leveraged a vulnerability within this contract, siphoning approximately $293 million in funds from the platform. The precision and scale of the exploit underscore the increasing imperative for rigorous auditing and continuous monitoring of smart contract infrastructure, especially those bridging assets across diverse blockchain environments.
Laundering and Conversion: The Trail of Stolen Funds
Following the massive theft, the perpetrator wasted no time in attempting to obscure the origins and destination of the illicit gains. According to Cyvers, the attacker utilized an address funded through Tornado Cash, a notorious cryptocurrency mixer. Tornado Cash, which has faced significant regulatory scrutiny and sanctions, allows users to anonymize transactions by pooling and mixing cryptocurrencies from various sources, making it exceptionally difficult to trace individual transfers.
This strategic use of a mixer is a common tactic employed by sophisticated cybercriminals in the crypto space, designed to complicate law enforcement and blockchain forensics efforts. Further compounding the challenge for recovery, Cyvers reported that approximately $250 million of the stolen funds had already been converted into Ether (ETH), the native cryptocurrency of the Ethereum layer-1 blockchain network. The rapid conversion to ETH suggests a move towards a more liquid and widely accepted asset, potentially in preparation for further dispersal or off-ramping. The remaining portion of the stolen funds is under active surveillance by security firms and relevant authorities, who are working to track its movement and identify potential avenues for recovery.

Immediate Fallout and Industry-Wide Repercussions
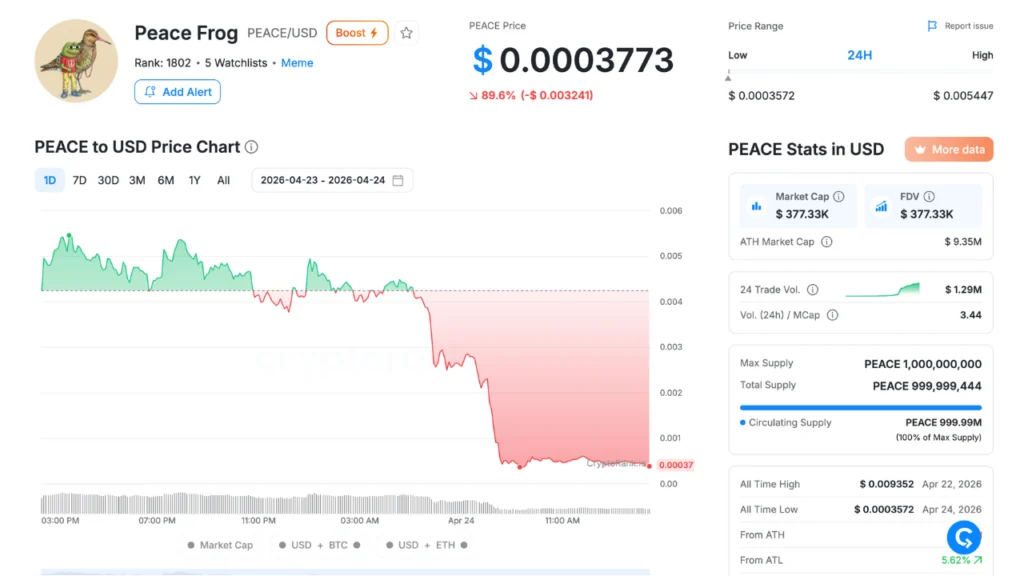
The ripple effects of the Kelp DAO hack were felt almost immediately across the interconnected DeFi landscape. Decentralized finance platform Aave, one of the largest lending and borrowing protocols, swiftly announced that it had "frozen rsETH markets on Aave V3 and V4" in direct response to the exploit. Aave’s decision highlights the systemic risks inherent in DeFi composability, where the failure or compromise of one protocol can necessitate protective measures across others that integrate or rely on its tokens.
Cyvers further indicated that at least nine other crypto protocols, having exposure to the rsETH token through various integrations, have also moved to freeze activity on their respective platforms. This rapid, cascading response underscores the fragility of trust and the speed at which contagion can spread within the DeFi ecosystem. Protocols are forced to prioritize user protection and market stability by isolating potentially compromised assets, even if it means temporarily disrupting normal operations.
Deddy Lavid, CEO of Cyvers, articulated the gravity of the situation, telling Cointelegraph, "This is exactly the kind of incident that highlights the risks of composability in DeFi." His statement serves as a stark reminder of the double-edged sword of composability – while it fosters innovation and creates powerful financial primitives, it also introduces complex interdependencies where a single point of failure can have widespread, detrimental consequences.
Understanding Liquid Restaking and its Vulnerabilities
Kelp DAO operates in the burgeoning sector of "liquid restaking," a novel DeFi primitive built atop Ethereum’s staking ecosystem. In traditional Ethereum staking, users lock up their ETH to support network security and earn rewards. Liquid staking protocols allow users to stake their ETH and receive a liquid derivative token (like rsETH), which can then be used in other DeFi applications (e.g., lending, borrowing, providing liquidity) while their underlying ETH remains staked. Liquid restaking extends this concept by allowing users to re-stake their liquid staking tokens with other protocols, further enhancing yield opportunities but also adding layers of complexity and potential risk.
The allure of higher yields has driven significant growth in the liquid restaking sector. However, each additional layer of abstraction and integration introduces new smart contracts and bridge mechanisms, each representing a potential attack surface. The rsETH adapter bridge, in this context, was a critical point of interaction between Kelp’s token and various blockchain environments, making it a high-value target for attackers seeking to exploit complex cross-chain logic.
A Disturbing Trend: Escalating Cybercrime in Web3

The Kelp DAO breach is not an isolated incident but rather the latest in a worrying succession of cybersecurity hacks and exploits that have plagued crypto platforms over recent months. The first quarter of 2026 alone witnessed staggering losses from Web3 hacks and scams, totaling approximately $482 million, according to various industry reports. This figure highlights an alarming trend of increasing financial impact from malicious activities in the blockchain space.
Just in April, the decentralized cryptocurrency exchange Drift Protocol suffered a massive exploit that drained approximately $280 million from its platform. The Drift attack presented a different, yet equally disturbing, facet of cybercrime: social engineering and suspected state-sponsored infiltration. The Drift Protocol team’s post-mortem update revealed that the attack involved "months of deliberate preparation," during which their team was allegedly infiltrated by suspected North Korean state-affiliated hackers. The attackers reportedly met Drift team members at a "major" crypto conference and collaborated with them for several months before deploying malware on developer machines and ultimately compromising the platform. This sophisticated, long-game approach signifies a new level of threat, moving beyond simple smart contract vulnerabilities to target human elements and organizational security.
While the Kelp DAO incident appears to be a direct smart contract exploit rather than an insider job or social engineering scheme, both events underscore the multifaceted and evolving nature of threats facing the DeFi space. Attackers are diversifying their methods, from exploiting technical flaws in code to manipulating human trust and organizational structures.
Implications for Security, Regulation, and User Trust
The persistent onslaught of large-scale hacks presents significant challenges for the future trajectory of decentralized finance. For protocol developers, it necessitates a paradigm shift towards even more robust security practices, including multi-layered auditing, bug bounty programs, formal verification of smart contracts, and real-time threat monitoring. The complexity of cross-chain bridges and liquid staking mechanisms demands a higher standard of due diligence and continuous vulnerability assessment.
Regulators globally are also keenly observing these incidents. The use of crypto mixers like Tornado Cash, coupled with massive financial losses, intensifies calls for stricter anti-money laundering (AML) and know-your-customer (KYC) regulations within the crypto sector. While DeFi proponents advocate for decentralization and privacy, the scale of these thefts inevitably draws attention from authorities concerned with financial crime and consumer protection. The challenge lies in finding a balance that fosters innovation without inadvertently creating fertile ground for illicit activities.
Perhaps most critically, these repeated breaches erode user trust, which is the bedrock of any financial system, decentralized or not. For DeFi to achieve mainstream adoption, it must demonstrate a consistent ability to safeguard user assets. Each major hack serves as a setback, reminding potential users of the inherent risks and the nascent stage of the technology. The industry faces an ongoing imperative to not only innovate but also to fortify its defenses, rebuild confidence, and educate users about the risks involved.
The Kelp DAO exploit, following closely on the heels of the Drift Protocol breach and other significant hacks, paints a clear picture of the ongoing cybersecurity arms race in the Web3 space. As protocols become more sophisticated and interconnected, so too do the methods of those seeking to exploit them. The incident is a stark reminder that while the promise of decentralized finance is immense, its journey to maturity is fraught with significant security challenges that demand constant vigilance, innovation, and collaboration across the entire ecosystem.