Despite this sharp decline in the total monetary value of stolen assets, the frequency of attacks remained remarkably consistent. Security analysts recorded roughly 160 successful exploits throughout 2023, a number nearly identical to the attack frequency seen in 2022. The divergence between the steady number of incidents and the falling value of the hauls suggests that while the threat landscape remains active, the effectiveness of the attacks has been curtailed by enhanced defensive measures, swifter incident response, and a more robust regulatory environment.
The Evolution of the Threat Landscape: From Smart Contracts to Infrastructure
In previous years, particularly during the "DeFi Summer" of 2020 and 2021, the majority of cryptocurrency thefts were attributed to vulnerabilities within smart contract code. Logic errors and flash loan attacks allowed exploiters to drain liquidity pools with surgical precision. However, 2023 marked a definitive shift in hacker methodology. Infrastructure attacks emerged as the most devastating category of cybercrime in the digital asset space, accounting for nearly 60% of the total value stolen throughout the year.
An infrastructure attack occurs when a malicious actor gains unauthorized access to a system’s underlying server architecture, private keys, or administrative credentials. These breaches are often more catastrophic than smart contract exploits because they bypass the protocol’s logic entirely, granting the attacker the same level of control as the system’s owners. In 2023, the average value of a single infrastructure-related breach rose to nearly $30 million, underscoring the high-stakes nature of centralized points of failure within decentralized ecosystems.
This trend highlights a critical irony in the industry’s development: while decentralized protocols have become more resilient to code-level bugs through rigorous auditing and formal verification, the human and organizational infrastructure surrounding these protocols remains a primary target for sophisticated social engineering and server-side compromises.
A Chronological Review of Major 2023 Exploits
The year 2023 was punctuated by several massive breaches that defined the security narrative. Each incident served as a stark reminder of the evolving tactics used by both independent hacker collectives and state-sponsored actors.
Q1: The Euler Finance Recovery
In March 2023, the Ethereum-based lending protocol Euler Finance fell victim to a flash loan attack that resulted in the loss of approximately $197 million. The attacker exploited a flaw in the protocol’s "donateToReserves" function. However, the Euler incident became a rare success story in the crypto security space. Through a combination of on-chain negotiation and the threat of law enforcement intervention, the hacker eventually returned nearly all of the stolen funds. This event demonstrated the growing efficacy of "on-chain diplomacy" and the increasing difficulty hackers face when attempting to launder large sums of stolen crypto.
Q2: The Multichain Crisis
The summer of 2023 was dominated by the collapse of Multichain, formerly one of the industry’s largest cross-chain bridges. In July, over $126 million in assets were drained from the bridge’s MPC (Multi-Party Computation) wallets. The incident was unique because it coincided with the disappearance of Multichain’s CEO, Zhaojun. It was later revealed that the CEO had sole control over the protocol’s servers and private keys, which were reportedly seized by Chinese authorities. This case highlighted the "key man risk" inherent in many protocols that claim to be decentralized but rely on centralized infrastructure.
Q3: The Mixin Network Breach
September saw one of the largest infrastructure attacks of the year when the Mixin Network, a decentralized cross-chain transfer protocol, lost approximately $200 million. The breach was attributed to a compromise of the protocol’s cloud service provider’s database. The Mixin hack was particularly notable because it targeted the custodial layer of the network, proving that even protocols designed for privacy and speed are vulnerable if their hosting infrastructure is not sufficiently hardened.
Q4: The Poloniex and HTX Ecosystem Attacks
The final quarter of 2023 was marked by a series of attacks on platforms linked to entrepreneur Justin Sun. In November, the Poloniex exchange suffered a hot wallet breach that saw roughly $114 million drained. Shortly thereafter, the HECO Bridge and the HTX (formerly Huobi) exchange were also targeted. These attacks were characterized by high speed and technical sophistication, leading many analysts to suspect the involvement of the Lazarus Group, a North Korean state-sponsored cybercrime unit known for its relentless focus on the cryptocurrency sector.
Data Analysis: Why Hack Volumes Are Trending Downward
The 50% reduction in stolen value is not a matter of luck but the result of a multi-pronged defensive strategy. TRM Labs’ research points to three primary factors contributing to the decline: improved security practices, intensified law enforcement pressure, and enhanced industry collaboration.
1. Heightened Security and Auditing Standards
The crypto industry has moved away from the "move fast and break things" ethos of its early days. Major protocols now undergo multiple third-party audits before deployment. Furthermore, the rise of bug bounty platforms like Immunefi has incentivized "white hat" hackers to report vulnerabilities rather than exploit them. In 2023 alone, bug bounties saved billions of dollars in potential losses by identifying critical flaws in advance.
2. The Law Enforcement "Pincer Movement"
International law enforcement agencies, including the FBI, the Department of Justice (DOJ), and Europol, have significantly increased their blockchain literacy. The 2023 takedown of ChipMixer—a darknet service used to launder stolen crypto—and the sanctioning of Sinbad.io by the U.S. Treasury’s Office of Foreign Assets Control (OFAC) have made it significantly harder for hackers to "off-ramp" their illicit gains into fiat currency. When the exit routes are blocked, the incentive to steal diminishes.
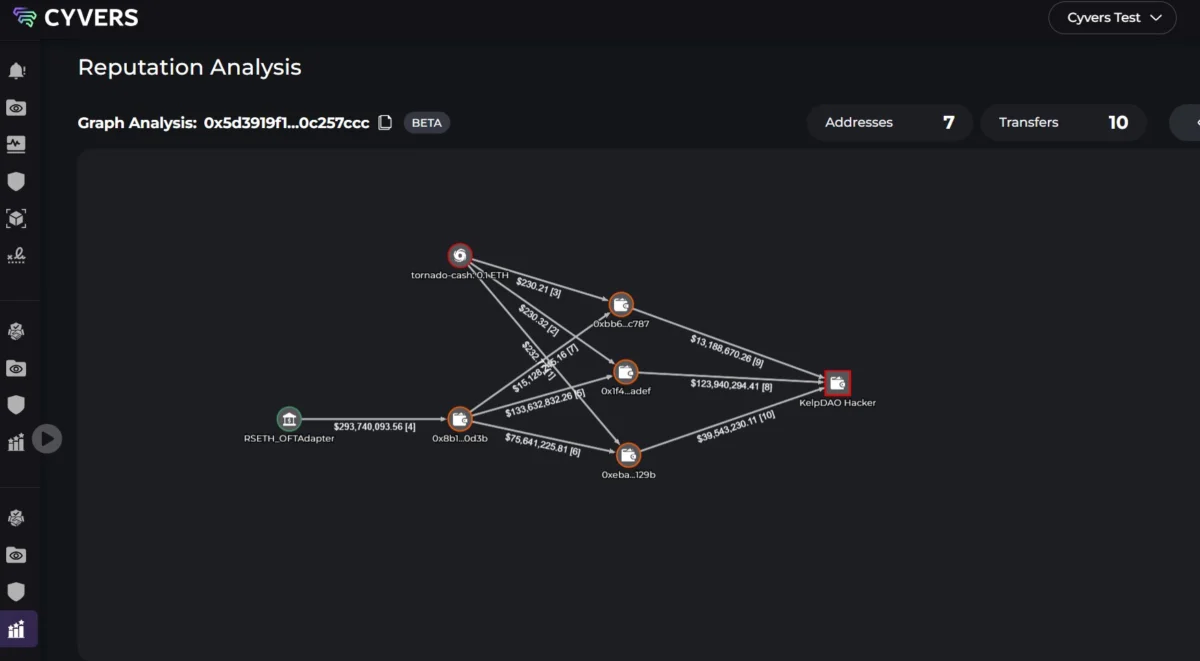
3. Real-Time Monitoring and Blacklisting
The industry has become more adept at responding to hacks in real-time. Stablecoin issuers like Tether (USDT) and Circle (USDC) now frequently freeze assets associated with known exploits. In 2023, the speed at which exchanges and asset issuers blacklisted hacker addresses increased dramatically, often rendering stolen funds useless within minutes of an attack.
Official Responses and Industry Sentiment
The decline in hack volumes has been met with cautious optimism by industry leaders and security experts. Ari Redbord, the Global Head of Policy at TRM Labs and a former federal prosecutor, noted that the industry’s ability to adapt is its greatest strength. "The decline in hack volumes is encouraging, but it is not a signal that we can relax," Redbord stated in the report. "The industry and law enforcement agencies need to remain vigilant and adaptable. They need to constantly be on the lookout for new threats and be prepared to adjust their security measures accordingly."
Conversely, some analysts argue that the decline in stolen value is partly a reflection of the "crypto winter." With lower total value locked (TVL) in many DeFi protocols compared to the 2021 peak, the "honeypots" available to hackers are smaller. However, security firms counter this by noting that even as market prices recovered in late 2023, the rate of large-scale thefts did not see a corresponding spike, suggesting that the defensive improvements are indeed structural rather than just market-dependent.
Broader Impact and Implications for the Future
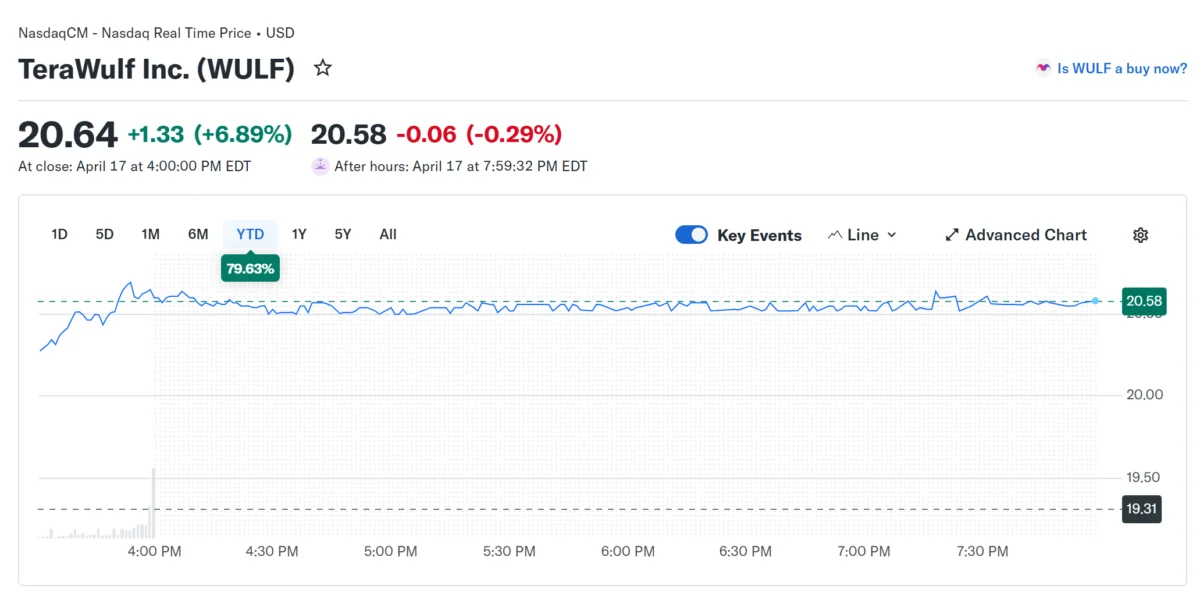
The reduction in successful high-value hacks has profound implications for the mainstream adoption of digital assets. One of the primary barriers to entry for institutional investors has been the perceived lack of safety and the absence of recourse in the event of a theft. As the industry proves it can defend itself and collaborate with regulators to recover funds, the path toward Exchange-Traded Funds (ETFs) and institutional custody becomes clearer.
However, the emergence of infrastructure attacks as the leading threat vector suggests that the next frontier of crypto security will not be in the code, but in the cloud. As protocols scale, they increasingly rely on centralized cloud providers like AWS or Google Cloud, creating new vulnerabilities that traditional cybersecurity measures must address.
Furthermore, the persistent threat of state-sponsored actors like the Lazarus Group remains a wildcard. These entities do not operate for profit alone but often for geopolitical leverage or to bypass international sanctions. Their methods are constantly evolving, moving toward social engineering, "spear-phishing" of developers, and the use of sophisticated AI-driven malware.
The success of 2023 in halving hack volumes provides a blueprint for the future: a combination of rigorous code audits, decentralized infrastructure to eliminate single points of failure, and a transparent relationship with global law enforcement. For the cryptocurrency market to reach its next stage of evolution, it must continue to prove that it is no longer an easy target for the world’s cybercriminals. The trend of 2023 is a promising start, but in the world of digital assets, the battle for security is a permanent state of affairs.