A Web3 wallet stands as a foundational gateway for individuals venturing into the rapidly expanding landscape of cryptocurrencies, Non-Fungible Tokens (NFTs), and decentralized applications (dApps). It represents a significant paradigm shift from traditional financial infrastructure, empowering users with direct control over their digital assets without the need for centralized intermediaries like banks or conventional crypto exchanges. This direct ownership is facilitated through the management of private keys, which are cryptographic proofs of asset control, fundamentally redefining financial autonomy in the digital age.
This comprehensive exploration delves into the mechanics of Web3 wallets, examines the diverse types available to users, and outlines essential security protocols for safeguarding digital assets within the Web3 ecosystem. The objective is to provide a clear, factual, and informative overview suitable for both novices and those seeking a deeper understanding of this critical technology.
The Dawn of Digital Autonomy: Understanding Web3 Wallets
At its core, a Web3 wallet is a digital tool designed to interact seamlessly with blockchain networks and decentralized applications. Unlike traditional banking systems where institutions hold and manage customer funds on their behalf, or even centralized cryptocurrency exchanges that act as custodians of users’ digital assets, a Web3 wallet places the user squarely in charge. This self-custodial nature is the defining characteristic, granting individuals complete sovereignty over their cryptocurrencies, NFTs, and other blockchain-based valuables.
The critical distinction lies in the concept of private keys. When digital assets are held on a centralized exchange, the platform typically controls the private keys associated with those assets, effectively acting as a custodian. In contrast, a Web3 wallet enables users to hold these private keys themselves. This direct possession of private keys means that only the user can authorize transactions, move funds, or interact with dApps, thus embodying the ethos of "being your own bank." This level of control is unprecedented in traditional finance and is a cornerstone of the decentralized web’s promise.
The functionalities afforded by a Web3 wallet extend far beyond mere storage. They serve as an individual’s digital identity within Web3, allowing for:
- Storage and Management: Securely holding various cryptocurrencies and digital assets.
- Sending and Receiving: Facilitating direct peer-to-peer transfers of digital assets globally.
- Interaction with dApps: Connecting to decentralized applications for activities like trading, lending, borrowing, gaming, and engaging with metaverse platforms.
- NFT Management: Displaying, trading, and minting Non-Fungible Tokens.
- Participation in Governance: Engaging with Decentralized Autonomous Organizations (DAOs) by voting on proposals using governance tokens.
- Identity Management: Potentially serving as a foundation for verifiable digital identity in the future.
While the majority of Web3 wallets are non-custodial, granting users full control over their funds and private keys, it is important to note that some services do offer custodial wallet options. In these cases, a third-party company manages the private keys on behalf of the user, offering convenience but reintroducing a degree of centralized trust. For true Web3 participation and adherence to its core principles, non-custodial solutions are generally preferred.
The Architecture of Decentralization: How Web3 Wallets Function
It is a common misconception that a Web3 wallet "stores" cryptocurrency in the same way a physical wallet holds cash. In reality, cryptocurrencies and other digital assets reside immutably on their respective blockchains. A Web3 wallet, instead, securely stores the cryptographic keys – specifically, the private keys – that prove ownership of these assets and enable their movement or interaction with smart contracts.
The operational backbone of a Web3 wallet relies on several interconnected components:
-
Key Pairs (Public and Private Keys): Every Web3 wallet generates a unique pair of cryptographic keys. The public key acts as the wallet’s address, similar to a bank account number, which can be shared freely for receiving funds. The private key, conversely, is a highly sensitive, secret alphanumeric code that functions as the digital signature to authorize transactions. It is the ultimate proof of ownership and control over the assets associated with the public address. Losing or compromising a private key means losing access to the associated assets forever.
-
Seed Phrase (Mnemonic Phrase): To simplify the backup and recovery process for complex private keys, most non-custodial Web3 wallets generate a "seed phrase" (also known as a mnemonic phrase). This is typically a sequence of 12 or 24 common words that can be used to regenerate all the private keys within a wallet. The seed phrase is the master key to a user’s digital kingdom; its security is paramount.
-
Blockchain Interaction: When a user initiates a transaction – whether sending cryptocurrency, buying an NFT, or interacting with a dApp – the Web3 wallet uses the private key to cryptographically "sign" the transaction. This signature verifies the user’s ownership and intent. The signed transaction is then broadcast to the relevant blockchain network, where miners or validators confirm its legitimacy and include it in a new block, making the transaction immutable and transparent.
-
Wallet Interface: This is the user-friendly application (mobile app, browser extension, desktop program) that provides an intuitive way to view balances, manage assets, and initiate transactions without needing to directly manipulate cryptographic keys. It translates complex blockchain operations into an accessible format.
-
WalletConnect and Similar Protocols: For interacting with dApps, many Web3 wallets utilize protocols like WalletConnect. This allows users to securely link their mobile or desktop wallets to various decentralized applications via QR codes or deep links, enabling seamless transaction signing directly from their personal device without exposing private keys to the dApp itself.
Together, these elements form a robust and secure ecosystem that allows users to engage with blockchain networks, facilitating the secure management and transfer of digital assets in a truly decentralized manner.
A Spectrum of Security and Convenience: Types of Web3 Wallets
Web3 wallets are not monolithic; they manifest in several forms, each offering a distinct balance of convenience, control, and security. The choice of wallet often depends on a user’s specific needs, the volume of assets they manage, and their technical proficiency.
Software Wallets (Hot Wallets)
Software wallets are the most ubiquitous and often the first point of entry for individuals exploring Web3. They exist as applications installed on internet-connected devices, hence the moniker "hot wallet." These include:
- Browser Extensions: Wallets like MetaMask, Phantom, and Keplr integrate directly into web browsers, allowing users to connect to dApps with ease while browsing the internet. They are highly convenient for frequent interactions with decentralized platforms.
- Mobile Applications: Wallets such as Trust Wallet, Coinbase Wallet (non-custodial version), and Argent offer similar functionalities on smartphones, providing on-the-go access to assets and dApps.
- Desktop Programs: Less common now, but some wallets offer standalone desktop applications for managing assets.
Advantages:

- Ease of Use: Generally straightforward to install and set up, making them ideal for beginners.
- Accessibility: Provide immediate access to funds and dApps from any internet-connected device.
- Cost-Effective: Most software wallets are free to download and use.
- Wide Compatibility: Support a broad range of cryptocurrencies and seamlessly integrate with a vast ecosystem of dApps.
Disadvantages:
- Online Vulnerability: As they are connected to the internet, software wallets are more susceptible to online threats such as hacking attempts, phishing scams, malware, and remote access exploits.
- Device Dependency: The security of the wallet is tied to the security of the device it’s installed on. If the device is compromised, the wallet can be too.
Hardware Wallets (Cold Wallets)
Hardware wallets are physical electronic devices designed to store private keys completely offline, making them the "gold standard" for Web3 wallet security. Roughly the size of a USB thumb drive, popular examples include Ledger and Trezor.
Advantages:
- Superior Security: By keeping private keys isolated from internet-connected devices, hardware wallets are virtually immune to online hacking, malware, and phishing attacks. Transactions are signed offline, and only the signed (but not the private key itself) is broadcast.
- Tamper-Proof Design: Often incorporate physical security features to prevent unauthorized access or manipulation.
- Physical Confirmation: Users must physically confirm transactions on the device’s screen, adding an extra layer of security against remote attacks.
- Ideal for Large Holdings: Recommended for storing significant amounts of cryptocurrency or valuable NFTs.
Disadvantages:
- Cost: Hardware wallets require an initial investment.
- Less Convenient: The process of connecting the device and confirming transactions can be slower than using a hot wallet, making them less practical for very frequent, small transactions.
- Risk of Physical Loss/Damage: While secure from cyber threats, they are vulnerable to physical loss, theft, or damage if not properly safeguarded.
Smart Contract Wallets (Account Abstraction)
Smart contract wallets represent a significant evolution in Web3 wallet technology. Built as smart contracts on the blockchain itself, rather than relying solely on a single private key, these wallets introduce advanced features and programmable logic. The concept, often referred to as "account abstraction," aims to bridge the gap between user experience and cryptographic security.
Advantages:
- Enhanced Security Features:
- Multi-Signature (Multi-sig): Requires multiple private keys to authorize a transaction, offering robust protection for shared funds or high-value assets.
- Social Recovery: Allows trusted individuals or devices to help recover access to a wallet if the primary key is lost, without exposing the private key to those individuals.
- Spending Limits: Programmable limits on daily or per-transaction spending.
- Time Locks: Delaying large transactions for a set period, allowing for intervention if unauthorized.
- Improved User Experience:
- Gas Abstraction: Potentially allows users to pay transaction fees in any token, or even have dApps sponsor gas fees, simplifying the user experience.
- Batch Transactions: Grouping multiple operations into a single transaction, reducing costs and complexity.
- Session Keys: Temporary keys with limited permissions for specific dApps, enhancing security during interactive sessions.
- Programmability: Offers flexibility for complex use cases, making them increasingly important for businesses, decentralized autonomous organizations (DAOs), and advanced blockchain applications.
Disadvantages:
- Complexity: Can be more complex to set up and understand than traditional key-based wallets.
- Blockchain Dependent: Relies on the security and functionality of the underlying blockchain network.
- Gas Costs: Deploying and interacting with smart contract wallets might incur higher gas fees initially.
- Newer Technology: Still evolving, with ongoing developments in standards and widespread adoption.
Paper Wallets
While less common now, paper wallets involve printing public and private keys (often as QR codes) onto a piece of paper. They offer extreme "cold storage" as they are completely disconnected from any digital system. However, they are highly impractical for regular use and carry risks like physical damage, loss, or theft, and the keys are typically not encrypted. They are generally considered outdated for most users in favor of hardware wallets.
Beyond Currency: The Multifaceted Utility of a Web3 Wallet
The capabilities of a Web3 wallet extend far beyond merely holding cryptocurrencies. It serves as an individual’s primary interface for navigating and participating in the decentralized web, offering a diverse array of functionalities that are continually expanding:
- Cryptocurrency Management: The most fundamental use case. Users can securely store, send, and receive a wide range of digital currencies across various blockchain networks. This includes popular assets like Bitcoin (BTC), Ethereum (ETH), and thousands of altcoins and stablecoins.
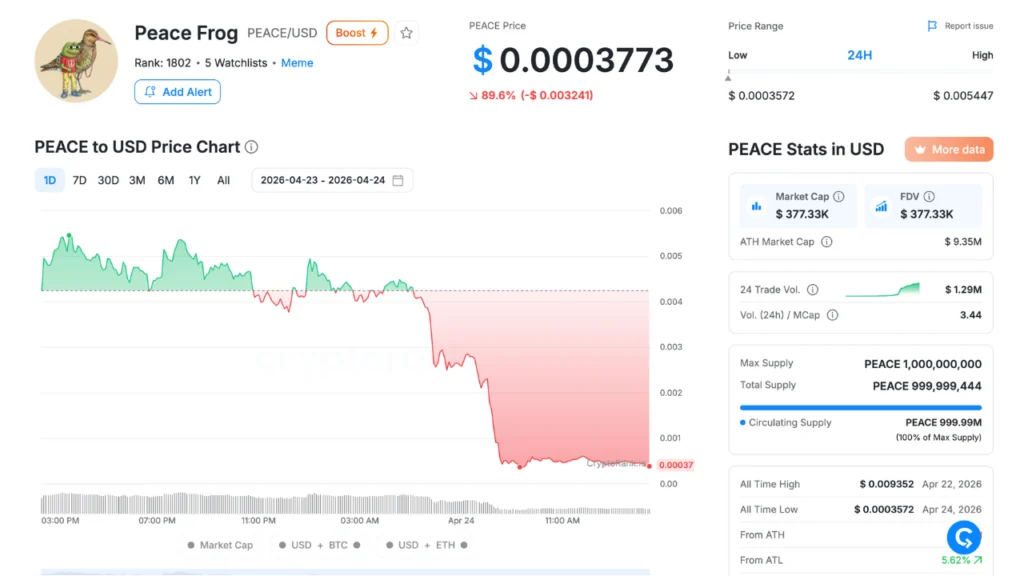
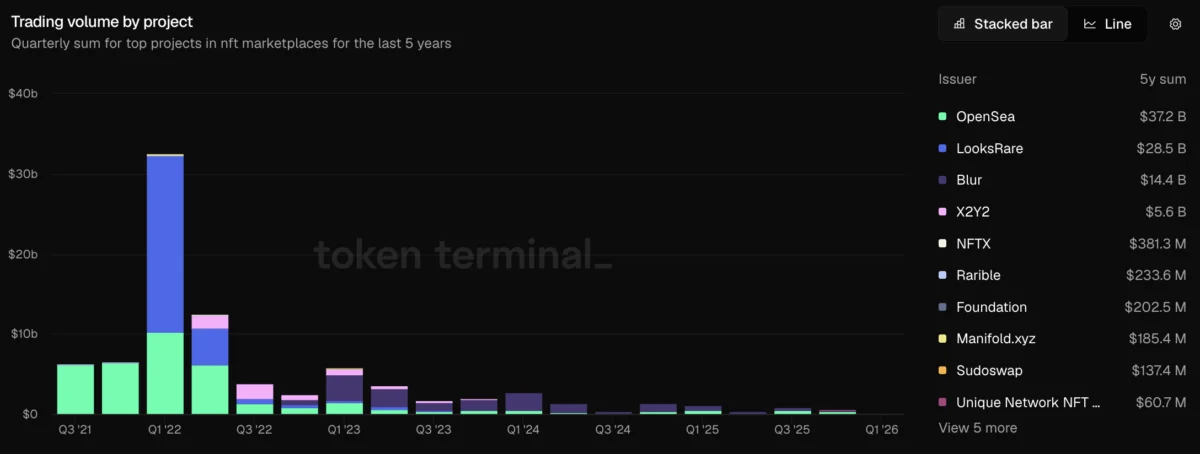
- NFTs and Digital Collectibles: Web3 wallets are essential for interacting with the burgeoning NFT market. Users can mint new NFTs, display their digital art and collectibles, and trade them on marketplaces like OpenSea or Rarible. The wallet acts as proof of ownership for these unique digital assets.
- Decentralized Applications (dApps) Interaction: This is where Web3 wallets truly shine. They enable seamless connection to a vast ecosystem of dApps spanning various sectors:
- Decentralized Finance (DeFi): Users can lend, borrow, stake, farm yield, and trade assets on platforms like Uniswap, Aave, and Compound, bypassing traditional financial institutions.
- GameFi and Play-to-Earn (P2E) Games: Wallets store in-game assets, characters, and rewards, allowing players to own and monetize their digital possessions.
- Metaverse Platforms: Accessing virtual worlds, purchasing virtual land, and interacting with other users and assets within metaverses.
- Decentralized Social Media: Engaging with new forms of social networking that give users more control over their data and content.
- Participation in Decentralized Autonomous Organizations (DAOs): For projects governed by DAOs, Web3 wallets hold governance tokens, allowing users to vote on proposals, influence project direction, and collectively manage shared treasuries. This represents a new model of organizational structure and democratic participation.
- Digital Identity and Verifiable Credentials: In the future, Web3 wallets are poised to become a hub for self-sovereign identity (SSI). Users could store verifiable credentials (e.g., educational degrees, professional certifications, government IDs) in their wallets, selectively revealing information without relying on centralized identity providers. This promises enhanced privacy and control over personal data.
- Subscription Management: Future iterations could see wallets managing decentralized subscriptions for digital services, replacing traditional payment methods tied to personal data.
As the Web3 ecosystem matures and integrates further into daily life, these wallets are expected to become the central nervous system for how individuals access financial tools, engage with online communities, assert digital ownership, and manage their personal data across an increasingly decentralized internet.
Navigating the Decentralized Landscape: Setting Up and Securing Your Web3 Wallet
Setting up a Web3 wallet is typically a straightforward process, but securing it requires diligent adherence to best practices. Given the non-custodial nature of most Web3 wallets, users bear the full responsibility for their digital asset security.
How to Set Up a Web3 Wallet (General Steps):
- Choose a Wallet: Select a reputable wallet that aligns with your needs (e.g., MetaMask for dApp interaction, Ledger for cold storage, Trust Wallet for mobile convenience).
- Download/Install: Obtain the official application or browser extension from the legitimate source (app store, official website). Be extremely wary of fake versions.
- Create a New Wallet: Select the option to "Create a new wallet." This will initiate the generation of your private keys and seed phrase.
- Secure Your Seed Phrase: This is the most critical step. The wallet will display your 12 or 24-word seed phrase. Write it down immediately on paper, accurately, and store it in multiple secure, offline locations. Never store it digitally (e.g., in a cloud service, email, or screenshot). Never share it with anyone.
- Confirm Seed Phrase: The wallet will usually ask you to re-enter parts of the seed phrase to ensure you’ve recorded it correctly.
- Set a Password/PIN: Establish a strong password for your software wallet or a PIN for your hardware wallet. This encrypts the wallet locally and prevents unauthorized access to the application itself.
- Explore and Fund: Once set up, your wallet is ready. You can now send cryptocurrencies to your public address or connect to dApps.
The Imperative of Security: Best Practices for Web3 Wallets
Given that Web3 wallets place full control (and responsibility) in the hands of the user, robust security measures are not optional but essential.
-
Guard Your Seed Phrase Above All Else:
- Offline Storage: Write it down on paper or engrave it on metal. Store it in a fireproof safe, a safety deposit box, or other physically secure locations.
- Multiple Backups: Consider creating multiple copies and storing them in geographically separate, secure locations.
- Never Digitalize: Do not store your seed phrase on a computer, phone, cloud service, or email. It makes it vulnerable to hacking.
- Never Share: No legitimate entity will ever ask for your seed phrase. Anyone who does is attempting to steal your assets.
-
Beware of Phishing and Scams:
- Verify URLs: Always double-check the URL of any website you connect your wallet to. Phishing sites mimic legitimate ones to steal your credentials or trick you into signing malicious transactions.
- Suspicious Links: Be extremely cautious of unsolicited emails, messages, or social media posts containing links that promise free crypto, exclusive NFTs, or urgent account updates.
- Fake Support: Scammers often impersonate customer support. Never give remote access to your computer or reveal your seed phrase.
-
Use Hardware Wallets for Significant Holdings: For any substantial amount of digital assets, a hardware wallet provides the highest level of security by isolating your private keys offline. Transfer smaller amounts to a software wallet for daily dApp interactions.
-
Scrutinize Transaction Details: Before confirming any transaction, carefully review all the details displayed by your wallet. Ensure the recipient address, amount, and contract interaction are exactly as intended. Malicious dApps or smart contracts can trick users into approving unintended actions.
-
Keep Software Updated: Regularly update your wallet software, browser, and operating system to benefit from the latest security patches.
-
Revoke Unused Approvals: When interacting with dApps, you often grant them "approvals" to spend certain tokens from your wallet. Regularly review and revoke approvals for dApps you no longer use or trust, especially those with unlimited spending allowances. Tools like Revoke.cash can help with this.

-
Use Strong, Unique Passwords: For software wallets, use complex, unique passwords that are not reused anywhere else. Consider a password manager.
-
Educate Yourself Continuously: The Web3 space evolves rapidly. Stay informed about new security threats, best practices, and technological advancements.
Key Players and Future Horizons: Popular Wallets and Emerging Trends
The Web3 wallet landscape is dynamic, with various providers competing on features, security, and user experience.
Leading Web3 Wallets (as of 2024, reflecting general trends):
- MetaMask: The most widely used browser extension wallet, particularly for the Ethereum ecosystem and EVM-compatible chains. Renowned for its extensive dApp compatibility.
- Trust Wallet: A popular mobile wallet supporting a vast array of cryptocurrencies and blockchains, known for its user-friendly interface.
- Ledger & Trezor: The dominant players in the hardware wallet market, offering top-tier security for large asset holdings.
- Coinbase Wallet: A non-custodial mobile wallet separate from the Coinbase exchange, offering broad asset support and dApp connectivity.
- Phantom: A leading browser extension and mobile wallet for the Solana ecosystem, known for its speed and NFT features.
- Argent: A smart contract wallet focusing on enhanced security features like social recovery and daily spending limits, offering a more user-friendly experience through account abstraction.
The Evolution of Wallet Technology and Future Horizons:
Web3 wallets are at the forefront of innovation, with developers continuously striving to enhance functionality, security, and user accessibility. The future of Web3 wallets is likely to be shaped by several key trends:
- Improved User Experience (Account Abstraction): This is perhaps the most significant area of development. Account abstraction aims to make Web3 wallets feel more like traditional banking apps, allowing for:
- Gasless Transactions: Users won’t need to hold specific network tokens (like ETH for Ethereum) to pay for transactions, potentially enabling dApps to sponsor gas or users to pay in any token.
- Social Recovery: Easier and more secure recovery options without relying on a single seed phrase.
- Batch Transactions: Combining multiple actions into one transaction for efficiency.
- Programmable Logic: Enabling complex, conditional transactions.
- Enhanced Interoperability: Wallets will increasingly support multiple blockchain networks (cross-chain compatibility) more seamlessly, simplifying asset management across the fragmented blockchain landscape.
- Self-Sovereign Identity (SSI) Integration: Wallets could become the digital hub for managing verifiable credentials and personal data, allowing users to control and selectively share their identity attributes without third-party custodians.
- Quantum Resistance: As quantum computing advances, cryptographic methods currently used by blockchains could become vulnerable. Future wallets may incorporate quantum-resistant algorithms to safeguard assets.
- Built-in On/Off-Ramps: Direct integration with fiat currencies (traditional money) will make it easier for users to convert between crypto and fiat within their wallets, reducing friction for new users.
- Hardware-Software Hybrid Solutions: More intuitive integration between the security of hardware wallets and the convenience of software interfaces.
- Regulatory Adaptation: As governments worldwide develop clearer regulations for digital assets, wallets will need to adapt to compliance requirements while maintaining decentralization.
With Web3 transitioning from niche to mainstream, wallets are poised to become the primary interface through which individuals interact with the decentralized internet, serving as their identity, financial tool, and access point to a new digital economy.
The Broader Implications: Web3 Wallets and the Future of the Internet
Web3 wallets represent more than just a technological advancement; they embody a philosophical shift towards individual empowerment and decentralization. Their widespread adoption carries profound implications for finance, digital ownership, and the very structure of the internet.
Firstly, they champion financial inclusion and independence. For billions globally who are unbanked or underbanked, Web3 wallets offer access to a global financial system without the prerequisites of traditional banking infrastructure. This direct access to lending, borrowing, and trading platforms can unlock economic opportunities previously unavailable. For everyone, they offer an escape from the fees, restrictions, and censorship often associated with centralized financial institutions.
Secondly, Web3 wallets are redefining digital ownership. In the Web2 paradigm, users "rent" their digital content and data from platforms like social media giants, often without true ownership. Web3, through NFTs and tokenized assets held in these wallets, allows individuals to genuinely own digital goods, art, music, and even parts of virtual worlds. This shift fundamentally alters the relationship between users and digital content, fostering a creator economy where ownership is verifiable and transferable.
Finally, they serve as the crucial bridge to a decentralized internet. As Web3 evolves, wallets are becoming the universal login for decentralized applications, replacing traditional usernames and passwords. This not only enhances security by eliminating single points of failure but also gives users greater control over their digital identity and privacy. The vision is an internet where users, not corporations, control their data and digital experiences.
However, this unprecedented control also comes with significant challenges. The responsibility for security shifts entirely to the user, meaning errors like losing a seed phrase can lead to irreversible asset loss. Scalability, regulatory clarity, and achieving mass adoption among non-technical users remain hurdles that the industry is actively working to overcome. Despite these challenges, the trajectory of Web3 wallets points towards a future where digital autonomy is not just a concept, but a tangible reality for internet users worldwide.
Conclusion
A Web3 wallet is an indispensable tool in the burgeoning blockchain ecosystem, serving as the primary interface for managing cryptocurrencies, storing other digital assets, and interacting with the vast array of decentralized applications. It fundamentally distinguishes itself from traditional financial accounts and centralized exchanges by granting individuals absolute control over their funds through the secure management of private keys and seed phrases.
This self-custodial model offers unparalleled independence and financial sovereignty, empowering users to participate directly in the decentralized web without relying on intermediaries. While this level of autonomy necessitates a heightened commitment to security, including diligent seed phrase protection, vigilance against phishing, and strategic use of hardware wallets for significant holdings, the benefits are transformative. With the right setup and adherence to robust security practices, a Web3 wallet empowers individuals to safely and effectively navigate the decentralized landscape, take full control of their digital assets, and actively shape their future in the digital economy. As Web3 continues its rapid expansion, these wallets will remain central to unlocking its full potential, serving as the personal gateways to a more open, transparent, and user-centric internet.
FAQs
Do I need a Web3 wallet to use DeFi?
Yes. Decentralized Finance (DeFi) platforms such as Uniswap, Aave, and Compound are built on blockchain networks and require a Web3 wallet to connect and interact. Your wallet acts as both your unique identifier and authorization mechanism, enabling you to lend, borrow, trade, or earn yield directly without the need to create traditional accounts or undergo extensive know-your-customer (KYC) processes with a centralized entity.
Is MetaMask a Web3 wallet?
Yes. MetaMask is one of the most widely recognized and popular Web3 wallets. It functions as a browser extension and mobile application, primarily used to connect to decentralized applications on the Ethereum blockchain and other Ethereum Virtual Machine (EVM)-compatible networks, allowing users to manage cryptocurrencies and interact with dApps.
What is the difference between a Web3 wallet and a bank account?
The fundamental difference lies in control and intermediation. A bank account is controlled by a financial institution; you trust the bank to hold and manage your funds, and they can impose restrictions, fees, and even freeze your assets. A Web3 wallet, conversely, gives you direct, self-custodial control of your funds via private keys, meaning you do not rely on any intermediary. You have instant, global access to your assets and can interact with decentralized applications without the restrictions and fees imposed by traditional banking systems.
Are Web3 wallets safe?
Web3 wallets are secure tools if proper precautions are meticulously followed. The security of your assets primarily depends on your diligence in protecting your private keys and seed phrases, avoiding phishing links, and understanding the risks of smart contract interactions. Hardware wallets offer the highest level of security for larger holdings by keeping private keys offline. Even if a wallet application is compromised, these fundamental security measures can prevent unauthorized access to your underlying assets.
What happens if I lose my seed phrase?
Losing your seed phrase (also known as a mnemonic phrase or recovery phrase) for a non-custodial Web3 wallet can permanently lock you out of your wallet and all the digital assets it controls. The seed phrase is the master key that can regenerate all your private keys. Without it, there is no way to recover access to your funds, as no central authority exists to assist you. It is essential to store your seed phrase offline in multiple secure, fireproof, and waterproof locations to prevent total loss.
Which Web3 wallet is best for beginners?
For beginners, software wallets like MetaMask, Trust Wallet, or Coinbase Wallet are generally recommended. They are relatively easy to set up, feature intuitive interfaces, and are widely supported across various DeFi and NFT platforms. They often provide clear guidance on managing tokens and safely storing seed phrases. As users accumulate more significant assets, transitioning to a hardware wallet like Ledger or Trezor for enhanced security is strongly advised.