The Midnight network is making significant waves in the burgeoning crypto industry, distinguishing itself through an innovative approach to harmonizing privacy, utility, and security. As a privacy-first blockchain, Midnight (NIGHT) is meticulously engineered to empower users with unprecedented control over their sensitive data, while simultaneously enabling private transactions, robust digital identity management, and compliant smart contract interactions. This article delves beyond the immediate hype surrounding Midnight to comprehensively explain its fundamental architecture, operational mechanisms, the critical problems it addresses, and its potential implications for the future of decentralized technologies, offering insights into whether an investment in the NIGHT token aligns with current market dynamics and individual risk appetites.
The Foundational Imperative: Addressing Blockchain’s Privacy Paradox
At its core, Midnight is a direct response to one of the most significant inherent limitations of traditional public blockchains: their pervasive data exposure. Networks like Bitcoin and Ethereum, while pioneering in their decentralization and immutability, operate on the principle of complete transparency. Virtually every transaction, wallet balance, and smart contract interaction is permanently etched onto a publicly accessible ledger. While this transparency is invaluable for auditability and fostering trust in a trustless environment, it simultaneously creates substantial hurdles for handling sensitive personal data, proprietary business logic, or confidential user information – scenarios commonplace in virtually every modern industry.
This paradox has long confined blockchain adoption in sectors demanding stringent data protection and regulatory compliance. Enterprises, healthcare providers, financial institutions, and even individual users are often hesitant to migrate critical operations or personal data to platforms where privacy is an afterthought. Midnight directly confronts this challenge by introducing "programmable privacy" – a paradigm where data can remain profoundly private while retaining on-chain verifiability. This innovative model shifts control to the application layer, allowing developers and users to selectively reveal only the information necessary for a specific interaction, rather than broadcasting every detail indiscriminately.
A Deeper Dive: What Defines Midnight (NIGHT)?
Midnight is not merely another privacy coin; it represents a sophisticated architectural evolution. Developed by Input Output Global (IOG), the driving force behind the Cardano blockchain, Midnight leverages a wealth of expertise in distributed systems and cryptographic research. Its design philosophy centers on creating a flexible and scalable environment where privacy is a configurable feature, not a rigid default.
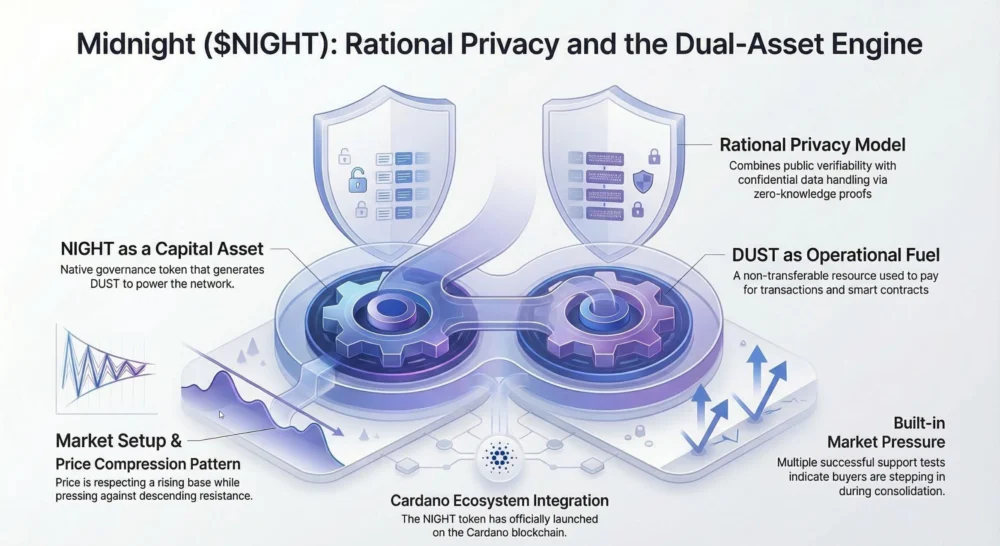
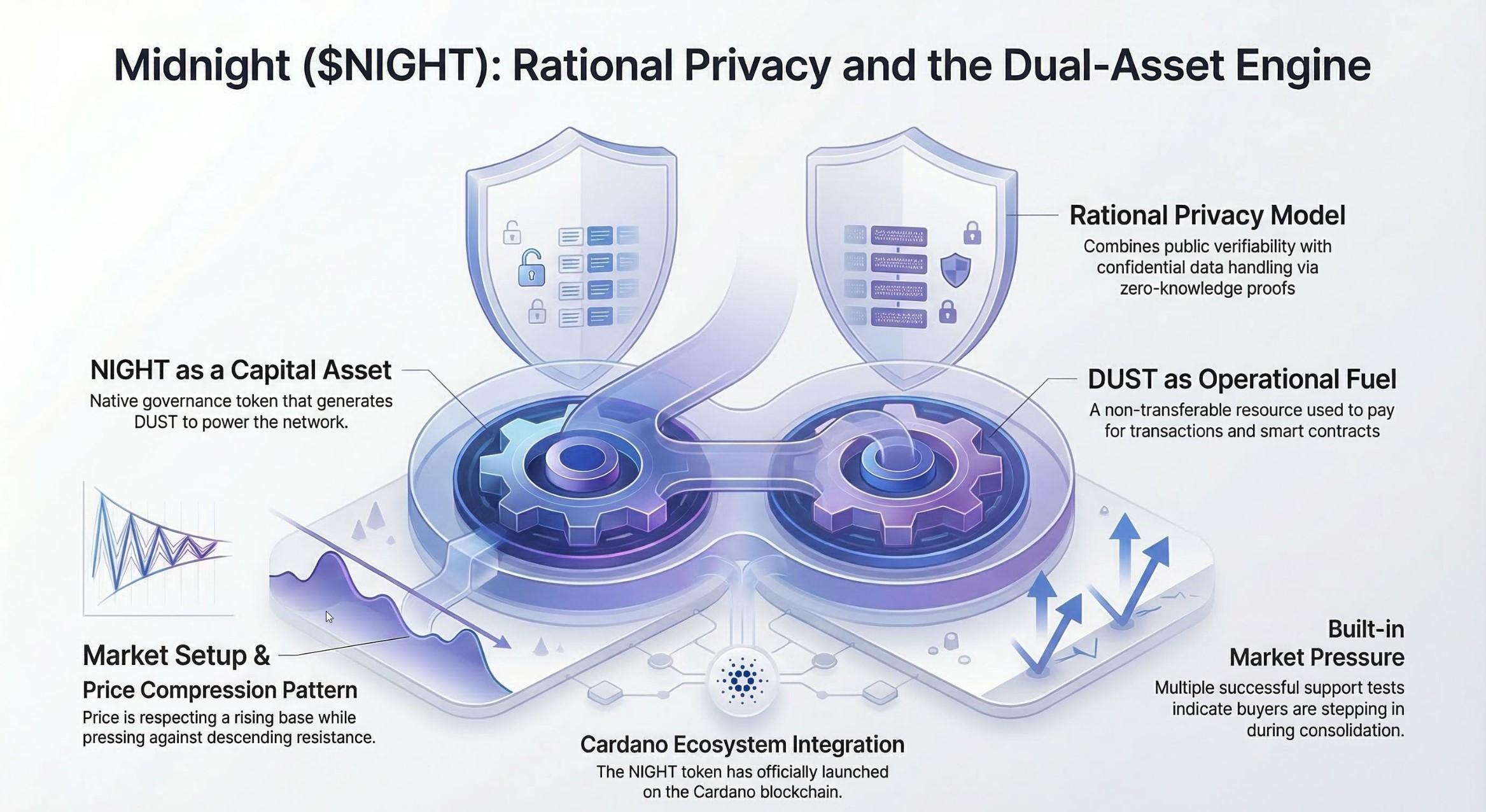
The native NIGHT token plays a multifaceted role within this ecosystem, serving as the primary governance token, underpinning the network’s security through staking mechanisms, and facilitating active participation in crucial network decisions. Midnight also employs a unique dual-token model, distinguishing it from the single-token economies prevalent across most blockchain platforms. This model separates the functions of network governance and transaction fee payment, a nuanced approach that will be explored in greater detail.
The Mechanics of Programmable Privacy: How Midnight Works
Midnight’s operational architecture is designed to achieve a delicate balance between public verifiability and private computation. It achieves this by intelligently separating the consensus layer from the private computation layer.
- Consensus Layer (Public): This layer maintains the network’s foundational security, settlement finality, and transaction verification. It ensures immutability and resistance to censorship, similar to traditional public blockchains, but it primarily deals with aggregated or proven public information, not raw sensitive data. Staking mechanisms for the NIGHT token operate within this public layer, securing the chain.
- Private Computation Layer (Encrypted): This is where the magic of privacy happens. Sensitive information and complex business logic are processed within an encrypted state, often stored locally on users’ devices or within secure enclaves. This separation allows users to interact with decentralized applications (dApps) without exposing every detail of their operations to the entire network.
This architectural division ensures that while the integrity and security of the blockchain are publicly verifiable, the confidentiality of user and application data remains paramount.

Zero-Knowledge Proofs (ZKPs): The Engine of Confidentiality
Central to Midnight’s ability to deliver programmable privacy are Zero-Knowledge Proofs (ZKPs). ZKPs are a cryptographic breakthrough that allows one party (the "prover") to prove to another party (the "verifier") that a statement is true, without revealing any information beyond the veracity of the statement itself.
In the context of Midnight, ZKPs empower developers to define precisely which information appears on the public ledger and which parts remain encrypted. For instance, a user can cryptographically prove they possess sufficient funds to complete a transaction without revealing their exact wallet balance. Similarly, they can prove they meet specific age requirements for an application without disclosing their date of birth, or verify their compliance with regulatory standards without exposing confidential personal details.
Midnight specifically relies on zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) for its ZKP implementation, facilitated by its proprietary Kachina protocol. zk-SNARKs are particularly valued for their conciseness and efficiency, generating small proof sizes that are quick to verify, making them suitable for handling large volumes of smart contract activity while upholding strong security and confidentiality guarantees. This technology is critical not only for privacy but also for enhancing blockchain scalability through concepts like zk-Rollups, which batch multiple transactions into a single ZKP for verification on the main chain.
Why ZKPs Are Indispensable for Modern Privacy Solutions
The importance of ZKPs extends far beyond theoretical cryptographic elegance; they are a cornerstone for real-world blockchain adoption, especially in industries burdened by stringent data protection and confidentiality requirements.
- Enhanced Privacy: ZKPs allow users and applications to interact pseudonymously or anonymously while still proving legitimacy, drastically reducing the digital footprint exposed on public ledgers.
- Regulatory Compliance: For sectors like finance (KYC/AML without revealing full identity), healthcare (secure patient data sharing under HIPAA), and legal services, ZKPs enable compliance by allowing proof of adherence to regulations without oversharing sensitive data. This fosters trust with regulators who often view full anonymity with suspicion.
- Reduced Data Leak Risk: By minimizing the amount of sensitive data stored on public, immutable ledgers, the attack surface for potential data breaches or deanonymization attempts is significantly reduced.
- Improved Scalability: Beyond privacy, ZKPs are instrumental in developing scalable blockchain solutions. By allowing complex computations to be performed off-chain and only a concise proof to be submitted on-chain, they reduce computational load and transaction costs, thereby improving overall network throughput.
Midnight’s Dual-Token Model: NIGHT & DUST Explained
While most blockchains consolidate all functions – governance, staking, and transaction fee payment – into a single native asset, Midnight employs a thoughtful dual-token system. This separation of concerns is a deliberate design choice aimed at enhancing network stability, utility, and user experience.
- NIGHT Token: This is the primary governance and staking token. It has a fixed supply, making it a scarce digital asset. Holders of NIGHT are empowered to participate in network governance decisions, vote on protocol upgrades, and contribute to the overall direction of the Midnight ecosystem. Furthermore, staking NIGHT tokens contributes to the network’s security and consensus mechanism, with stakers earning rewards for their participation. Critically, holding NIGHT tokens automatically generates DUST, effectively providing a renewable resource for network activity.
- DUST Token: Unlike NIGHT, DUST is not a tradable or transferable asset. It functions purely as the internal resource used to pay for transaction fees and smart contract operations within the Midnight network. Conceptually, DUST acts like a rechargeable battery or an "energy unit" for running applications on Midnight. Its generation is tied directly to NIGHT holdings, meaning active participants who secure the network (by staking NIGHT) are inherently rewarded with the means to interact with it. This model aims to create a sustainable economy where network usage is directly linked to network participation, preventing speculative attacks on gas fees and ensuring predictable operational costs for developers and users.
This dual-token model aims to insulate the network’s operational costs from the speculative volatility often associated with governance tokens, providing a more stable and predictable environment for dApp developers and users.
NIGHT Tokenomics and Strategic Allocation
The NIGHT token, as the backbone of Midnight’s governance and security, features a fixed maximum supply of 24 billion tokens. The current circulating supply hovers around 16.6 billion, a figure subject to dynamic changes based on vesting schedules and allocation strategies.
While specific granular details of the allocation often reside within detailed whitepapers, common crypto tokenomics principles suggest a distribution designed to foster decentralization, incentivize early adoption, reward development, and ensure long-term sustainability. Typical allocation categories for a project of this scale might include:
- Ecosystem Development Fund: To support grants, partnerships, and developer incentives.
- Team and Advisors: Vested over time to align long-term interests with project success.
- Foundation/Treasury Reserve: For ongoing operational costs, marketing, and strategic investments.
- Public/Private Sale: To fund initial development and provide liquidity.
- Staking Rewards: To incentivize network security participants.
NIGHT’s primary utilities include:
- Staking for Consensus Security: Securing the network and earning rewards.
- Governance Voting: Participating in proposals and decision-making for protocol evolution.
- Treasury Decisions: Influencing the allocation of community funds.
- DUST Generation: Providing the renewable resource for transaction fees.
This structured tokenomics framework, detailed in the Midnight tokenomics and incentives whitepaper, is designed to align incentives across all stakeholders – users, developers, validators, and investors – towards the long-term health and growth of the network.
Transformative Potential: Real-World Applications of Midnight
Midnight’s programmable privacy features are poised to unlock a vast array of real-world applications previously deemed incompatible with public blockchain technology. Its ability to selectively reveal data addresses critical industry pain points:
- Financial Services:
- Private DeFi: Enabling confidential transactions, private derivatives trading, and credit scoring without exposing sensitive financial positions.
- Compliant KYC/AML: Financial institutions can verify a user’s identity and compliance status using ZKPs without requiring the user to disclose their full personal information to every service provider.
- Secure Inter-institutional Data Sharing: Banks can share confidential market data or risk assessments without revealing proprietary strategies.
- Healthcare:
- Confidential Patient Records: Securely sharing patient data between authorized providers for diagnosis or treatment, while maintaining patient privacy and compliance with regulations like HIPAA.
- Clinical Trials: Managing sensitive research data confidentially, ensuring data integrity and participant anonymity.
- Supply Chain Management:
- Private Logistics Tracking: Tracking sensitive goods or components along a supply chain without revealing proprietary routes or customer information to competitors.
- Counterfeit Prevention: Verifying product authenticity at each stage without exposing the entire supply chain network.
- Digital Identity and Credentials:
- Self-Sovereign Identity (SSI): Users can hold and manage their digital identities, selectively disclosing verifiable credentials (e.g., age, educational qualifications, professional licenses) without relying on centralized authorities or exposing underlying personal data.
- Private Access Control: Granting access to digital services or physical locations based on verified attributes, without revealing the full identity of the accessor.
- Enterprise Solutions:
- Confidential Business Logic: Companies can deploy dApps with proprietary business rules and data on-chain without exposing their intellectual property.
- Private Voting Systems: Secure and verifiable corporate or organizational voting, where individual votes remain private but the final tally is auditable.
By providing a robust and flexible privacy layer, Midnight aims to bridge the gap between the transparency of public blockchains and the confidentiality requirements of real-world enterprises and individuals, fostering wider adoption of decentralized technologies.
The Future Horizon: Midnight’s Strategic Roadmap
Looking ahead, Midnight is strategically positioned to become a foundational privacy layer for the broader Web3 ecosystem. Its roadmap outlines ambitious milestones designed to transition the project from its developmental stages to a fully functional, decentralized network.
A critical near-term milestone is the federated mainnet launch, currently anticipated in late March 2026. This launch will mark the transition from test environments to a production chain, enabling the deployment of early private smart contracts and dApps. A "federated" launch typically implies an initial phase with a pre-defined or consortium-based set of validators, which then gradually transitions towards full decentralization with broader validator participation.
Beyond the initial mainnet launch, Midnight plans a significant expansion of its decentralization efforts, notably by attracting Cardano stake pool operators. This strategic move leverages the established and robust Cardano ecosystem, integrating experienced validators and fostering synergy between the two IOG-developed networks. This collaboration could bring significant security and community benefits to Midnight.
Further down the roadmap, Midnight is pushing towards achieving full cross-chain interoperability by late 2026. If successful, this would allow hybrid applications to operate seamlessly across various blockchain ecosystems, such as Ethereum and Solana, while preserving Midnight’s core privacy features. Such interoperability is crucial for expanding Midnight’s reach and utility, allowing developers to build privacy-enhanced solutions that can interact with the vast liquidity and user bases of other major chains.
From a market perspective, some analysts and proponents anticipate that Midnight (NIGHT) could see significant appreciation as its mainnet proves its utility and gains traction. The successful deployment of privacy-preserving dApps and the attraction of enterprise users would be key catalysts. However, the crypto market remains highly volatile. Risks include potential delays in the roadmap, large supply unlocks of the NIGHT token over time (which can exert downward pressure on price), intense competition from other privacy-focused or ZKP-centric projects, and the inherent challenge of attracting a critical mass of developers and real-world use cases at scale.
Conclusion: Investment Considerations for Midnight (NIGHT)
The decision to invest in NIGHT ultimately hinges on an individual’s conviction regarding privacy as an indispensable foundational layer for the next generation of blockchain applications. Midnight squarely addresses critical limitations of current public blockchains, specifically concerning exposed sensitive data, friction with regulatory frameworks, and inadequate privacy models for complex use cases. Its dedicated focus on private smart contracts, verifiable digital identity, and compliant applications has the potential to attract a diverse cohort of developers and enterprise users, creating a powerful network effect.
However, as with any digital asset, investing in NIGHT is not without substantial risks. The cryptocurrency market is notorious for its extreme volatility, and Midnight, as a relatively new project with significant milestones ahead, is particularly susceptible. Future supply unlocks and vesting schedules could introduce selling pressure. Furthermore, the network still needs to achieve demonstrable product-market fit and prove its long-term viability against a backdrop of increasing competition in the privacy space.
Prospective investors are strongly advised to conduct thorough due diligence, assess their personal risk tolerance, and ensure that any investment in NIGHT aligns with their broader financial strategy. It is paramount to never invest more capital than one is prepared to lose.
Frequently Asked Questions (FAQs)
Is NIGHT a good investment in 2024/2025/2026?
Whether NIGHT is a suitable investment depends heavily on your individual risk tolerance and your belief in the long-term necessity of programmable privacy in the blockchain space. Currently, there is speculative upside potential tied to the anticipated March 2026 mainnet launch, which could serve as a significant catalyst. However, this is balanced by inherent risks such as extreme market volatility, future token unlocks from various allocation categories, and intense competition from established zero-knowledge (ZK) chains and other privacy-focused protocols. Some market sentiments suggest a cautious approach, advising investors to await post-launch stability and demonstrable utility rather than chasing current speculative movements.
What is the NIGHT token price prediction for 2026?
Predictions for NIGHT’s price in 2026 are largely speculative and vary widely. Realistically, more conservative models might project price levels in the range of $0.04-$0.05, particularly if token unlocks create selling pressure or if the mainnet launch faces unexpected challenges. Conversely, optimistic scenarios suggest the token could trade between $0.13-$0.35 by year-end 2026, contingent on a successful mainnet deployment, strong dApp adoption, and significant utility growth. Average projections tend to hover around $0.05-$0.07, with higher valuations requiring sustained ecosystem development and proven real-world impact. These predictions are highly sensitive to market conditions and project execution.
How is Midnight different from Monero and Zcash?
Monero and Zcash are pioneering privacy coins known for obscuring nearly all transaction details by default, utilizing techniques like ring signatures, stealth addresses, and ZK-SNARKs (in Zcash’s case) to provide a high degree of anonymity. Midnight differentiates itself through a "selective disclosure" or "programmable privacy" approach. Instead of obscuring everything by default, Midnight uses zero-knowledge proofs to allow applications and users to choose which information remains private and which can be revealed for specific purposes, such as regulatory compliance, auditing, or fulfilling specific business logic. This nuanced approach aims to provide flexibility and compliance, making it potentially more palatable for enterprise and regulated environments that require a balance between privacy and accountability.
Where can I buy NIGHT tokens?
NIGHT tokens are typically available for purchase on several major centralized cryptocurrency exchanges (CEXs) such as OKX, Bybit, KuCoin, Gate.io, and Binance. Availability can vary by region and exchange. Additionally, depending on the ecosystem’s development and bridge infrastructure, NIGHT may also be accessible on certain decentralized exchanges (DEXs), often via bridges connected to the Cardano ecosystem. It is always recommended to verify the legitimacy and security of any exchange before conducting transactions.