In the rapidly evolving landscape of digital finance, the private key stands as the singular, indispensable element governing ownership, control, and security over cryptocurrency assets. Whether an individual is initiating a transaction, receiving funds, or simply holding digital currencies, this cryptographically generated alphanumeric code is the ultimate proof of ownership, granting unfettered control over a digital wallet and its contents. This article delves into the intricate mechanics and profound significance of private keys, exploring their operational framework, their pivotal role in safeguarding digital wealth, the inherent threats they face, and the essential strategies for robust private key management in an increasingly decentralized financial ecosystem.
The Foundational Layer: What Exactly is a Private Key?
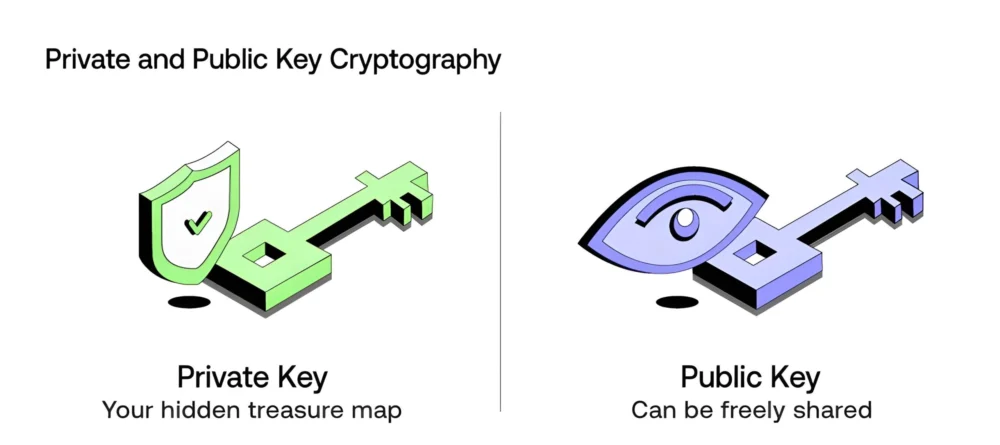
At its core, a private key is a secret cryptographic string, typically a 256-bit number, that serves as the lynchpin for accessing and managing assets within a cryptocurrency wallet. It is not merely a password; rather, it is a fundamental component of an asymmetric cryptographic system, generated with the creation of a digital wallet. This lengthy, pseudo-random code forms a unique pair with a public key, derived from the private key through a one-way mathematical function, most commonly elliptic curve multiplication (ECDSA) in prominent blockchains like Bitcoin and Ethereum. While the public key, which can be openly shared and is used to generate wallet addresses for receiving funds, acts as a public identifier, the private key must remain absolutely confidential. Its secrecy is paramount, as anyone possessing the private key gains complete and irreversible control over the associated digital assets, akin to having the physical keys to a vault containing immense wealth.
The genesis of this cryptographic architecture dates back to the 1970s with the pioneering work on public-key cryptography, notably by Whitfield Diffie and Martin Hellman, and independently by RSA. These innovations laid the groundwork for secure digital communication and, eventually, for the decentralized ownership models seen in blockchain technology. The application of these principles in cryptocurrencies introduced a paradigm shift, enabling individuals to self-custody their financial assets without reliance on intermediaries, a concept directly enabled and secured by the private key.
The Mechanics of Asymmetric Cryptography: How Private Keys Function
The operational elegance of a private key lies in its symbiotic relationship with its public counterpart within the framework of asymmetric cryptography. This system is designed so that the public key can be mathematically derived from the private key, but the reverse — deriving the private key from the public key — is computationally infeasible, effectively rendering it impossible with current technology. This unidirectional derivation is crucial for security.
When a cryptocurrency transaction is initiated, the private key is employed to create a unique digital signature. This signature is not an encryption of the entire transaction data but rather a cryptographic proof that the holder of the private key has authorized the action. The public key then serves to verify this signature across the blockchain network without ever revealing the private key itself. The network’s nodes confirm the validity of the signature using the public key, ensuring that the transaction originated from the legitimate owner of the funds and has not been tampered with. This process guarantees both authenticity and integrity, forming the bedrock of trust in a trustless system. For instance, a Bitcoin private key is a 256-bit number, resulting in approximately 2^256 possible keys. To put this into perspective, this number is vastly larger than the number of atoms in the observable universe, making brute-force attacks practically impossible.
The Unseen Guardian: Benefits of Private Key Encryption
While often discussed in the context of cryptocurrencies, the principles underpinning private key encryption offer broader benefits across various digital security domains:
- Performance and Speed: Private key encryption, particularly symmetric encryption where the same key is used for both encryption and decryption, is renowned for its efficiency. When processing large volumes of data, symmetric algorithms require fewer computational steps compared to asymmetric methods, leading to faster data throughput. This efficiency is critical in high-volume environments, ensuring rapid encryption and decryption while maintaining robust security.
- Data Integrity: Beyond mere secrecy, private key systems are instrumental in preserving data integrity. By cryptographically signing data with a private key, any subsequent alteration, however minor, will invalidate the signature. The receiving party, using the corresponding public key, can instantly detect if the information has been tampered with during transmission. This mechanism is vital for ensuring the reliability and trustworthiness of digital communications and transactions.
- Confidentiality: The most intuitive benefit of private key encryption is confidentiality. By ensuring that the secret key is known exclusively to authorized parties, encrypted messages and data remain inaccessible to unauthorized entities. As long as the private key remains secure and uncompromised, sensitive information is shielded from exposure, a critical component for privacy in the digital age.
- Authentication and Non-Repudiation: When combined with public key cryptography, private keys provide powerful tools for authentication. Digital signatures generated with a private key serve as irrefutable proof of identity and consent. The ability for anyone with the public key to verify that a message originated from a specific private key holder, and that the holder cannot later deny having sent it (non-repudiation), is fundamental to legal and financial digital agreements.
Private Keys in Action: Beyond Cryptocurrency Wallets

While their role in cryptocurrency is arguably their most high-profile application, private keys are integral to numerous other secure digital systems:
- Decrypting Messages or Data: In secure communication protocols, a sender might encrypt a message using the recipient’s public key. Only the recipient, possessing the corresponding private key, can then decrypt and read the original message. This ensures secure, confidential exchanges, a principle widely used in email encryption (e.g., PGP) and secure messaging applications.
- Creating Digital Signatures for Documents: Beyond financial transactions, private keys are used to digitally sign documents, software, and other digital assets. This process provides authenticity, ensuring that a file originated from a verified source and has not been altered since it was signed. This is crucial for software updates, legal documents, and intellectual property protection.
- Accessing Secure Systems (SSL/TLS): Private keys are fundamental to establishing secure connections over the internet, notably through SSL/TLS certificates. Websites use a private key stored on their server, paired with a public key embedded in an SSL certificate, to encrypt traffic between the server and a user’s browser. This protects sensitive data exchanged online, such as login credentials and financial information, from eavesdropping and tampering.
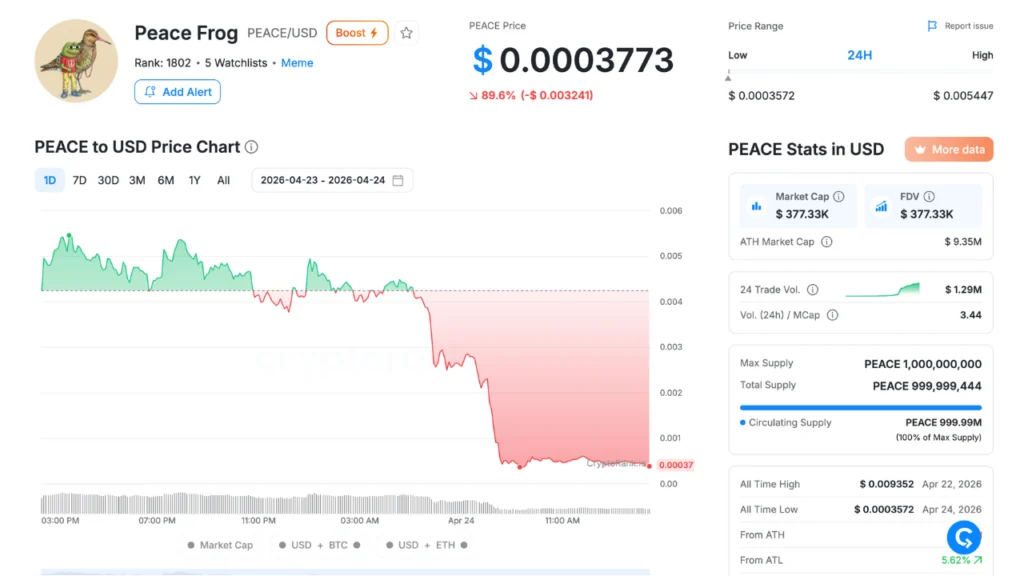
- Authorizing Cryptocurrency Transactions: This remains the most direct and impactful application. When a user wishes to send Bitcoin, Ethereum, or any other cryptocurrency, their wallet utilizes the private key to sign the transaction. This digital signature is broadcast to the network, which then verifies it using the public key before confirming the transfer of funds. The loss of this private key directly equates to the irreversible loss of access to the associated cryptocurrency. This stark reality drives the emphasis on secure storage solutions like hardware wallets (e.g., Ledger Nano X, Trezor) which keep private keys isolated from internet-connected devices. Industry data suggests that billions of dollars in cryptocurrency have been lost due to compromised or lost private keys, underscoring the critical need for robust management.
The Immutable Truth: Private Keys vs. Public Keys
The distinction between private and public keys is central to understanding blockchain security and digital asset ownership. While they are mathematically linked, their roles and required levels of secrecy are diametrically opposed.
| Aspect | Public Key | Private Key |
|---|---|---|
| Visibility | Can be openly shared with anyone. | Must be kept absolutely secret and never exposed. |
| Primary Role | Encrypts data, verifies digital signatures, derives wallet addresses. | Decrypts data, creates digital signatures, authorizes transactions. |
| Generation | Mathematically derived from the private key via a one-way function. | Generated first, typically as a random 256-bit number, forming the source of the pair. |
| Usage Example | Used to receive cryptocurrency (like a bank account number) or verify the authenticity of a sender. | Used to spend cryptocurrency, access funds, or prove ownership of digital assets. |
| Security Risk | Sharing poses no direct risk to funds. | If compromised, results in immediate and irreversible loss of associated funds. |
| Computational Intensity | Verification and derivation can be computationally intensive, especially for complex signature schemes. | Operations like signing are generally faster and more direct. |
Private Keys vs. Passwords: A Fundamental Distinction
Many new entrants to the crypto space mistakenly equate private keys with traditional passwords. However, their nature, function, and security implications are profoundly different.
| Aspect | Private Key | Password |
|---|---|---|
| Type | A cryptographic string (e.g., a 256-bit number or its base58 representation). | A human-readable string of characters, chosen by the user. |
| Usage | Directly signs transactions, proves ownership of assets, controls digital identity. | Authenticates access to an account, service, or device. |
| Storage | Ideally stored offline (cold storage), encrypted on user devices, or within hardware security modules. Never shared. | Often stored (hashed) on remote servers; can be written down or remembered. |
| Security Model | Asymmetric cryptography; irreversible control. Loss means permanent loss of assets. | Symmetric or shared secret; relies on centralized systems for authentication; vulnerable to various attacks. |
| Recoverability | None. A lost private key (without a backup seed phrase) results in permanent, irreversible loss of assets. | Often resettable via email, SMS, security questions, or customer support. |
| Vulnerability | Theft or exposure grants full, immediate control over assets. | Brute-force attacks, keylogging, phishing, dictionary attacks, credential stuffing, database breaches. |
| Crypto Relevance | Essential for self-custody and direct interaction with blockchain networks (e.g., hardware wallets, DeFi protocols). | Primarily protects logins to centralized exchanges or web services; does not directly secure on-chain funds. |
The Perilous Landscape: Threats to Private Keys
The absolute power a private key wields makes it a prime target for malicious actors. Understanding the common threats is the first step toward effective mitigation:
- Phishing Attacks: Sophisticated social engineering schemes designed to trick users into revealing their private keys or seed phrases. This often involves fake websites, emails, or messages masquerading as legitimate entities (e.g., wallet providers, exchanges) to solicit sensitive information.
- Malware and Keyloggers: Malicious software installed on a user’s device can monitor keystrokes, steal clipboard data, or directly access files where private keys might be stored. Ransomware can also encrypt a user’s data, including wallet files, demanding payment for their release.
- Physical Theft or Loss: Hardware wallets, which store private keys offline, are vulnerable to physical theft or accidental loss. If the device is stolen and not adequately secured (e.g., with a strong PIN), or if the recovery seed phrase is also compromised, funds can be lost.
- Insecure Storage Practices: Storing private keys on internet-connected devices (hot wallets), on cloud services without robust encryption, or simply writing them on unsecured paper without proper backups significantly increases vulnerability. Screenshots, text files, or easily discoverable notes are common pitfalls.
- Social Engineering: Beyond phishing, attackers might manipulate individuals into granting remote access to their computers, installing malicious software, or directly revealing their keys through deceptive conversations.
- Supply Chain Attacks: Less common but potentially devastating, these involve compromising the manufacturing or distribution process of hardware wallets or other security devices, embedding malicious code that could compromise keys.
Safeguarding Digital Wealth: Private Key Management Strategies
Given the irreversible consequences of a compromised or lost private key, robust management is not merely advisable but absolutely essential. The industry has converged on several best practices:
Challenges:
- Human Error: Forgetting keys, misplacing backups, or making typos during transcription are common human errors that lead to loss.
- Technical Complexity: Understanding the nuances of different wallet types, backup methods, and cryptographic principles can be daunting for non-technical users.
- Security vs. Convenience Trade-off: Highly secure methods (e.g., air-gapped cold storage) are often less convenient for frequent transactions, pushing users towards riskier hot wallets.
- Evolving Threat Landscape: Cybercriminals constantly adapt their tactics, requiring continuous vigilance and updates to security practices.
How to Keep Your Keys Secure:

- Prioritize Cold Storage: For significant holdings, cold wallets (hardware wallets like Ledger, Trezor, or air-gapped computers) are the gold standard. These devices keep private keys entirely offline, meaning they are never exposed to internet-connected threats. Transactions are signed on the device, with only the signed transaction broadcast to the network.
- Secure Seed Phrase Backups: Most modern wallets use a BIP39-compliant seed phrase (a sequence of 12 or 24 words) from which all private keys can be deterministically derived. This seed phrase is your ultimate backup. It should be:
- Written Down: On paper or metal, not digitally stored (no screenshots, text files, or cloud storage).
- Stored in Multiple Secure, Diversified Locations: Avoid keeping all backups in one place. Consider a fireproof safe, a bank vault, or separate physical locations.
- Protected from Physical Damage: Laminated, etched in metal, or stored in waterproof/fireproof containers.
- Never Shared: Treat your seed phrase with the same secrecy as your private key.
- Use Multi-Signature (Multi-Sig) Wallets: For shared funds or enhanced security, multi-sig wallets require multiple private keys to authorize a transaction. For example, a "2-of-3" multi-sig wallet needs two out of three designated private keys to sign off on any transaction. This provides redundancy and prevents a single point of failure.
- Employ Strong Encryption and Password Practices: While private keys are distinct from passwords, strong passwords are vital for securing any software wallets, exchange accounts, or devices that might interact with your crypto. Use unique, complex passwords and two-factor authentication (2FA) for all accounts.
- Be Wary of Phishing and Social Engineering: Always verify the authenticity of websites, emails, and messages. Never click suspicious links or download attachments from unknown sources. Legitimate services will never ask for your private key or seed phrase.
- Regular Security Audits and Updates: Keep all software (operating systems, antivirus, wallet applications) updated to patch known vulnerabilities. Regularly review your security practices and adapt them as new threats emerge.
- Education and Awareness: The most potent defense is an informed user. Understanding the technology, the risks, and the best practices is crucial for navigating the digital asset space safely.
The Broader Implications: Self-Custody and the Future of Digital Assets
The private key is more than just a security feature; it is the embodiment of financial sovereignty and decentralization. It empowers individuals to be their own bank, removing the need for trusted third parties. This paradigm shift, however, comes with significant responsibility. The rise of DeFi (Decentralized Finance) further underscores the importance of private key management, as users directly interact with protocols, lending, borrowing, and swapping assets without intermediaries.
From a regulatory perspective, the concept of self-custody presents unique challenges and opportunities. Governments and financial institutions grapple with how to regulate an ecosystem where ultimate control resides with the individual private key holder. As the digital asset market continues to mature, with a global market capitalization often exceeding trillions of dollars, the robustness of private key security will remain a central determinant of its long-term viability and mainstream adoption. Industry experts consistently advocate for user education and the development of more intuitive, yet secure, key management solutions to bridge the gap between technical complexity and widespread usability.
Conclusion
The private key stands as the bedrock of security and ownership in the cryptocurrency world, a powerful cryptographic construct that grants unparalleled control over digital assets. It is the core element that enables individuals to truly own their wealth in a decentralized manner, facilitating secure transactions, proving identity through digital signatures, and safeguarding confidentiality. While offering immense benefits, this power comes with the critical responsibility of meticulous private key management. By understanding its fundamental role, recognizing the pervasive threats, and diligently adhering to best practices such as cold storage, secure backups, and unwavering vigilance against cyber threats, users can navigate the digital asset landscape securely, protecting their financial autonomy in this transformative era.
FAQs
How can I see my private key?
Most cryptocurrency wallets, especially software wallets, offer an option within their settings to view or export your private key. For hardware wallets, the key is generated and stored securely offline, and the device provides a method (usually involving a recovery seed phrase) to safely reveal it for backup purposes. However, exposing your private key outside a secure environment dramatically increases the risk of theft. It’s generally advised against viewing it unless absolutely necessary for backup or migration, and even then, to do so in an air-gapped (offline) environment.
Can a private key be hacked?
Yes, a private key can be compromised or "hacked" indirectly. While the mathematical complexity makes brute-forcing a private key virtually impossible, it can be stolen through various attack vectors. These include malware (keyloggers, clipboard hijackers) on internet-connected devices, phishing attacks that trick users into revealing it, social engineering, or physical theft of devices where the key or its backup (seed phrase) is stored insecurely. Storing keys offline in hardware wallets significantly reduces these risks.
How do I recover my private key if lost?
A private key, once lost without a prior backup, cannot be recovered. This is why proper private key management emphasizes creating secure backups, typically in the form of a seed phrase. If you lose your device or forget your private key, your seed phrase is the only way to restore access to your funds. Without it, the associated cryptocurrency is permanently inaccessible and effectively lost.
Is a password the same as a private key?
No. A password is a human-readable string used for authentication to an account or device, and it can usually be reset. A private key, in contrast, is a cryptographic string (a very large number) that directly proves ownership and authorizes transactions on a blockchain. Losing a password might mean temporary inconvenience; losing a private key (or its seed phrase backup) means permanent loss of your cryptocurrency funds.
What’s the difference between a private key and a seed phrase?
A private key is a single, unique cryptographic key that directly controls access to a specific cryptocurrency address and its funds. A seed phrase (also known as a recovery phrase or mnemonic phrase) is a sequence of 12, 18, or 24 words that serves as a master backup for all the private keys within a hierarchical deterministic (HD) wallet. If you have your seed phrase, you can regenerate all your private keys and restore access to all associated wallets and funds, even if your original wallet device is lost or destroyed.