The global cryptocurrency ecosystem faced an unprecedented wave of illicit activity throughout 2025, resulting in a record-breaking $2.7 billion stolen through high-profile hacks and sophisticated exploits. This figure, compiled and verified by leading blockchain-monitoring firms including Chainalysis, TRM Labs, and the Web3 security platform De.Fi, represents the highest annual loss in the history of digital assets. The surge in criminal activity was characterized not only by the sheer volume of capital lost but also by the increasing dominance of state-sponsored actors and the vulnerability of both centralized exchanges and decentralized finance (DeFi) protocols. As the industry grapples with these losses, the 2025 data underscores a growing arms race between cyber-adversaries and the security professionals tasked with defending the burgeoning digital economy.
The Bybit Breach: A Landmark in Financial Crime
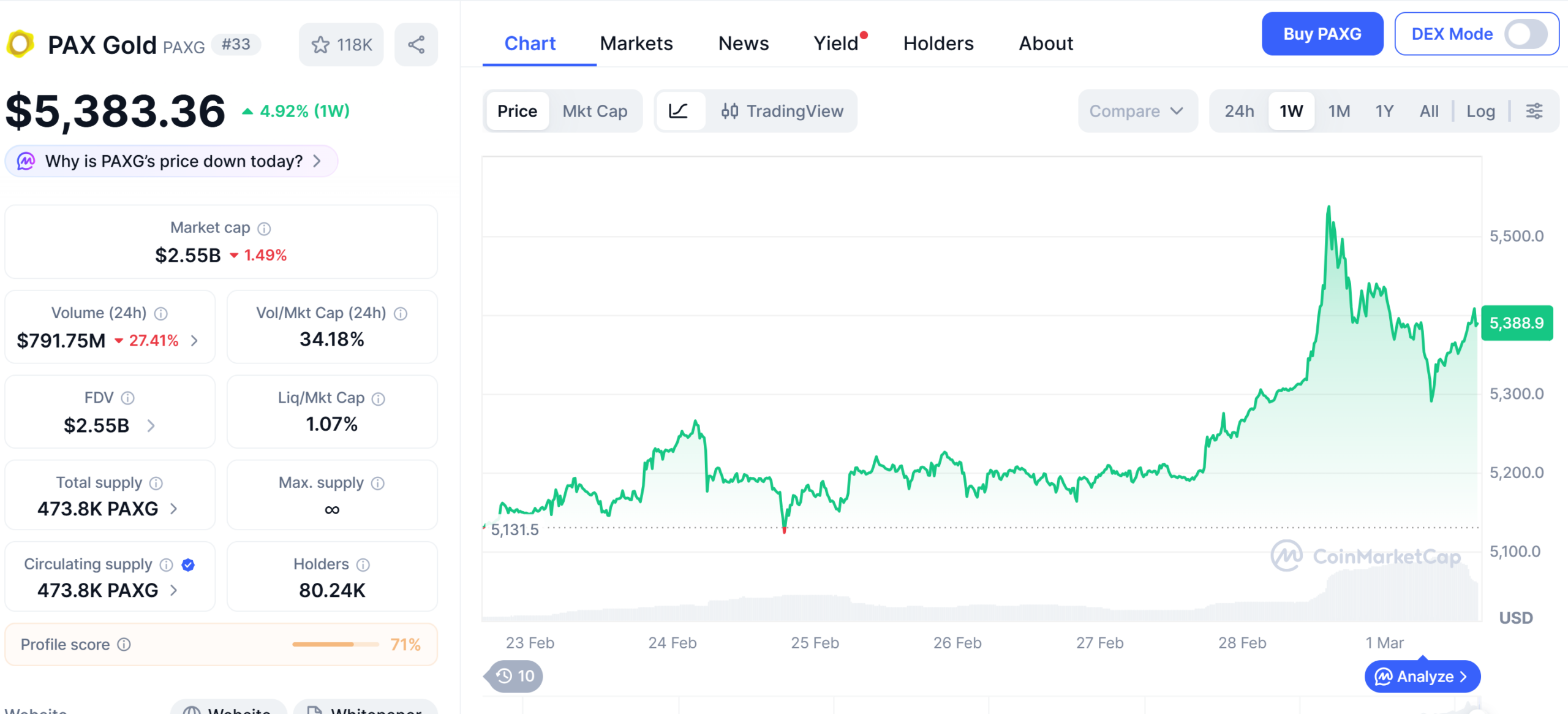
The defining moment of the year occurred in February 2025, when the Dubai-based cryptocurrency exchange Bybit fell victim to a catastrophic security breach. In a single coordinated strike, hackers managed to exfiltrate approximately $1.4 billion in various digital assets. This event instantly rewrote the history of cybercrime, becoming the largest known cryptocurrency heist of all time and one of the most significant financial robberies in human history. To put the scale of the Bybit loss into perspective, it nearly doubled the previous record held by the 2022 exploit of the Ronin Network, which saw $624 million stolen.
Investigations into the Bybit incident were swift and involved a multi-agency effort. Blockchain analysis firms, which track the movement of stolen funds through public ledgers, quickly identified patterns consistent with the Lazarus Group, a notorious hacking collective linked to the North Korean government. These findings were later corroborated by the Federal Bureau of Investigation (FBI), which officially attributed the heist to the Democratic People’s Republic of Korea (DPRK). The breach was reportedly executed through a combination of sophisticated social engineering targeting high-level employees and the compromise of the exchange’s private key management system. The aftermath of the Bybit hack sent shockwaves through the global market, leading to heightened scrutiny of how centralized exchanges (CEXs) secure their "hot" and "cold" storage solutions.
The Dominance of North Korean State Actors
While various criminal groups were active throughout 2025, the North Korean government remained the most prolific and successful force in the realm of crypto-theft. According to data shared by Chainalysis and Elliptic, hackers operating on behalf of the Kim Jong Un regime were responsible for at least $2 billion of the $2.7 billion total stolen during the year. This continues a long-standing trend of state-sponsored cyber-warfare used to circumvent international sanctions and generate hard currency.
Since 2017, North Korean hackers have stolen an estimated $6 billion in cryptocurrency. The strategic importance of these thefts cannot be overstated; international intelligence agencies and the United Nations have repeatedly warned that these illicit funds are directly funneled into the DPRK’s sanctioned nuclear weapons and ballistic missile programs. The 2025 data suggests that North Korea has refined its tactics, moving away from simple phishing attempts toward more complex "long-con" social engineering, where hackers pose as recruiters or technical support staff to gain deep access to internal corporate networks.
A Chronology of Major 2025 Exploits
Beyond the massive Bybit heist, 2025 was punctuated by several other significant breaches that highlighted the diverse vulnerabilities within the Web3 space. These incidents targeted a range of platforms, from decentralized exchanges (DEXs) to liquidity protocols.
The Cetus Protocol Exploit
In May 2025, Cetus, a prominent decentralized exchange and liquidity provider, suffered a major security breach. Hackers exploited a vulnerability in the protocol’s smart contract logic, allowing them to drain approximately $223 million. This incident served as a stark reminder that even audited smart contracts can harbor "zero-day" vulnerabilities that sophisticated attackers can identify and weaponize.
The Balancer Rounding Error
Later in the year, Balancer, an automated market maker and decentralized investment platform built on the Ethereum blockchain, reported a loss of $128 million. Security researchers at Check Point identified that the attacker utilized a "rounding error" exploitation technique. By manipulating the mathematical calculations used to determine asset ratios during large swaps, the attacker was able to slowly but surely bleed the protocol’s liquidity pools. This type of "logic hack" is increasingly common in DeFi, where the complexity of financial math provides ample opportunities for exploitation.
The Phemex Hot Wallet Incident
The centralized exchange Phemex also reported a significant security incident involving its hot wallet infrastructure. Cybercriminals successfully bypassed security layers to steal more than $73 million in assets. While the exchange moved quickly to reimburse affected users and bolster its defenses, the event highlighted the persistent risks associated with keeping large amounts of liquidity in internet-connected wallets.
Comparative Data and the Escalation of Theft
The $2.7 billion stolen in 2025 marks a steady and concerning upward trend in cryptocurrency crime. To understand the gravity of the current situation, one must look at the data from previous years:
- 2023: Approximately $2 billion was stolen through hacks and exploits.
- 2024: The figure rose to $2.2 billion, a 10% increase year-over-year.
- 2025: The total jumped to $2.7 billion, representing a nearly 23% increase from the previous year.
While the total value stolen has increased, some analysts point out that the number of individual incidents has actually fluctuated. This suggests that hackers are becoming more selective, focusing their efforts on "whale" targets—large exchanges and protocols with billions in Total Value Locked (TVL)—where the payoff for a successful breach is monumental. Additionally, Chainalysis tracked an additional $700,000 stolen from individual private wallets through "drainer" scripts and personal phishing attacks, indicating that while the headlines are dominated by institutional losses, retail investors remain constant targets.
Official Responses and Industry Reaction
The scale of the 2025 thefts has prompted a more aggressive stance from international regulators and law enforcement. The FBI’s direct attribution of the Bybit hack to North Korea was accompanied by a series of advisories aimed at crypto-native firms, urging them to implement more rigorous multi-signature (multi-sig) requirements and to conduct frequent, unannounced security audits.
In the private sector, the reaction has been a mixture of alarm and innovation. "The record-breaking nature of 2025 is a wake-up call for the entire industry," stated a spokesperson for TRM Labs. "We are seeing a shift where security is no longer just a checkbox for compliance, but a fundamental requirement for survival. The sophistication of the Lazarus Group and other state actors means that traditional cybersecurity measures are no longer sufficient."
Many DeFi projects have responded by adopting "circuit breaker" mechanisms—automated systems that pause all protocol activity if a suspicious outflow of funds is detected. Furthermore, there has been a significant push toward the adoption of "Insurance-as-a-Service" within the Web3 ecosystem, allowing protocols to pool resources to provide a safety net for users in the event of a hack.
Broader Impact and Future Implications
The long-term implications of a $2.7 billion loss year are multifaceted. For institutional investors, the persistent threat of theft remains a primary barrier to entry. While the approval of various crypto-linked financial products in traditional markets has brought more liquidity to the space, the "Wild West" nature of crypto-security continues to give pause to conservative asset managers.
Moreover, the geopolitical ramifications of North Korea’s success in this arena are profound. As the DPRK continues to use stolen crypto to fund its military ambitions, the digital asset industry finds itself inadvertently entangled in global security concerns. This has led to calls for more stringent Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations across the board, including for decentralized protocols that have historically resisted such measures.
As 2025 draws to a close, the cryptocurrency industry stands at a crossroads. The record losses have proven that the current infrastructure is still vulnerable to determined and well-funded adversaries. However, the resilience of the market—which saw total market capitalization remain relatively stable despite these heists—suggests an enduring belief in the underlying technology. The lessons learned from the Bybit, Cetus, and Balancer hacks will likely dictate the security standards of the next generation of blockchain applications, as the industry seeks to move past its most expensive year to date.