The global cryptocurrency landscape underwent a seismic shift in its security profile throughout 2023, characterized by a dramatic reduction in the total value of digital assets lost to malicious actors. According to comprehensive data compiled by blockchain intelligence firm TRM Labs and corroborated by various decentralized finance (DeFi) security monitors, the total value of stolen cryptocurrency plummeted by more than 50% compared to the previous year. While 2022 was defined by catastrophic losses exceeding $3.8 billion, the 2023 calendar year saw this figure retract to approximately $1.85 billion. This sharp decline suggests that the combined efforts of heightened protocol security, increased law enforcement intervention, and improved industry transparency are beginning to yield tangible results in the ongoing battle against cybercrime.
Despite the significant reduction in the total monetary value of stolen assets, the frequency of attacks remained remarkably consistent. Security researchers tracked approximately 160 individual hacking incidents throughout 2023, a number that mirrors the attack frequency of 2022. This discrepancy between the number of incidents and the total value lost indicates a shift in the effectiveness of the attacks or a pivot in the targets chosen by hackers. It further suggests that while the "success rate" of penetrating systems remains high, the "yield" per attack has diminished, likely due to better asset management practices and the implementation of more robust emergency response protocols by exchange operators and DeFi developers.
The Dominance of Infrastructure Attacks
The 2023 security report highlights a critical evolution in the methodology of cybercriminals. Infrastructure attacks emerged as the most devastating category of exploit, accounting for nearly 60% of the total value stolen during the year. Unlike smart contract exploits, which target vulnerabilities in the code of a specific decentralized application, infrastructure attacks involve gaining unauthorized access to the underlying systems of a crypto project. This often includes compromising private keys, stealing administrative credentials, or infiltrating the servers that host a platform’s core operations.
The average loss per infrastructure incident reached a staggering $30 million, a figure that underscores the high-stakes nature of these breaches. These attacks are typically the result of sophisticated social engineering, phishing campaigns, or zero-day vulnerabilities in third-party software. By bypassing the blockchain’s inherent cryptographic security and targeting the human or server-side elements of a project, hackers are able to drain massive pools of liquidity in a single event. The prevalence of these attacks in 2023 has forced many organizations to rethink their internal security hierarchies, moving toward multi-signature requirements and hardware-based key management systems to mitigate the risk of a single point of failure.
A Chronological Review of 2023’s Major Exploits
The year began with a series of high-profile incidents that initially suggested 2023 might follow the dark trend of its predecessor. In March, the DeFi lending protocol Euler Finance was hit by a flash loan attack that resulted in the theft of approximately $197 million. However, this incident also provided a rare glimmer of hope for the industry when, following intense negotiations and the involvement of law enforcement, the attacker eventually returned nearly all of the stolen funds. This "white hat" resolution set a precedent for the year, showing that the transparency of the blockchain can sometimes be used as leverage to recover assets.

By mid-year, the focus shifted toward cross-chain vulnerabilities. In July, the Multichain protocol suffered a massive outflow of funds totaling over $126 million. The incident was shrouded in mystery and controversy, particularly following reports that the project’s CEO had been detained by Chinese authorities and that the private keys to the protocol’s MPC (Multi-Party Computation) wallets were under centralized control. This event served as a stark reminder of the risks associated with centralized points of failure in supposedly decentralized systems.
The third quarter saw one of the largest infrastructure breaches of the year when the Mixin Network, a decentralized cross-chain transfer protocol, lost $200 million in September. The attack targeted the cloud service provider used by the network, once again highlighting the vulnerability of crypto projects to traditional IT infrastructure failures. The year’s major exploits concluded in November with a $126 million hack of the Poloniex exchange. This attack was particularly notable for the speed at which the funds were moved and swapped across various decentralized exchanges, a hallmark of sophisticated state-sponsored or professional hacking groups.
Factors Driving the Decline in Stolen Value
Industry analysts, including TRM Labs’ Head of Legal and Government Affairs, Ari Redbord, attribute the downward trend in hack volumes to a multi-pronged evolution in the crypto ecosystem. One of the primary drivers is the increased sophistication of law enforcement agencies globally. Organizations such as the FBI, the Department of Justice (DOJ), and international bodies like Europol have significantly enhanced their blockchain forensics capabilities. The successful seizure of assets and the tracking of funds through complex mixing services have made it increasingly difficult for hackers to "off-ramp" their stolen gains into fiat currency.
Furthermore, the industry itself has adopted a more proactive stance toward security. In 2023, the use of real-time monitoring tools and "circuit breakers"—mechanisms that automatically pause a protocol if suspicious activity is detected—became more widespread. The "DeFi" sector, which was the primary target of hackers in 2022, saw a marked improvement in code auditing practices. Project developers are now more likely to undergo multiple third-party audits and maintain active bug bounty programs, incentivizing ethical hackers to identify and report vulnerabilities before they can be exploited by malicious actors.
The regulatory environment has also played a crucial role. As jurisdictions around the world, including the European Union with its MiCA (Markets in Crypto-Assets) regulation, begin to implement clearer frameworks, crypto service providers are being held to higher standards of custodial security. This regulatory pressure has led to the adoption of institutional-grade security measures that were previously absent in the retail-focused crypto market.
The Role of State-Sponsored Actors and Mixers
While the overall value of stolen funds decreased, the activity of state-sponsored groups, most notably the North Korean-linked Lazarus Group, remained a significant threat. These actors are known for their persistence and their ability to execute highly complex infrastructure attacks. In 2023, law enforcement made significant strides in disrupting the tools used by these groups to launder money. The US Treasury’s Office of Foreign Assets Control (OFAC) sanctioned several high-profile "mixers," such as Sinbad.io, which were allegedly used to obfuscate the trail of funds from the Axie Infinity and Harmony Bridge hacks.

The crackdown on these mixing services has created a "liquidity bottleneck" for cybercriminals. Without reliable ways to wash stolen assets, the utility of the theft is greatly reduced. This has forced hackers to hold onto stolen assets for longer periods or attempt riskier conversion methods, increasing the likelihood of their eventual identification and the recovery of the funds.
Broader Implications and the Path Forward
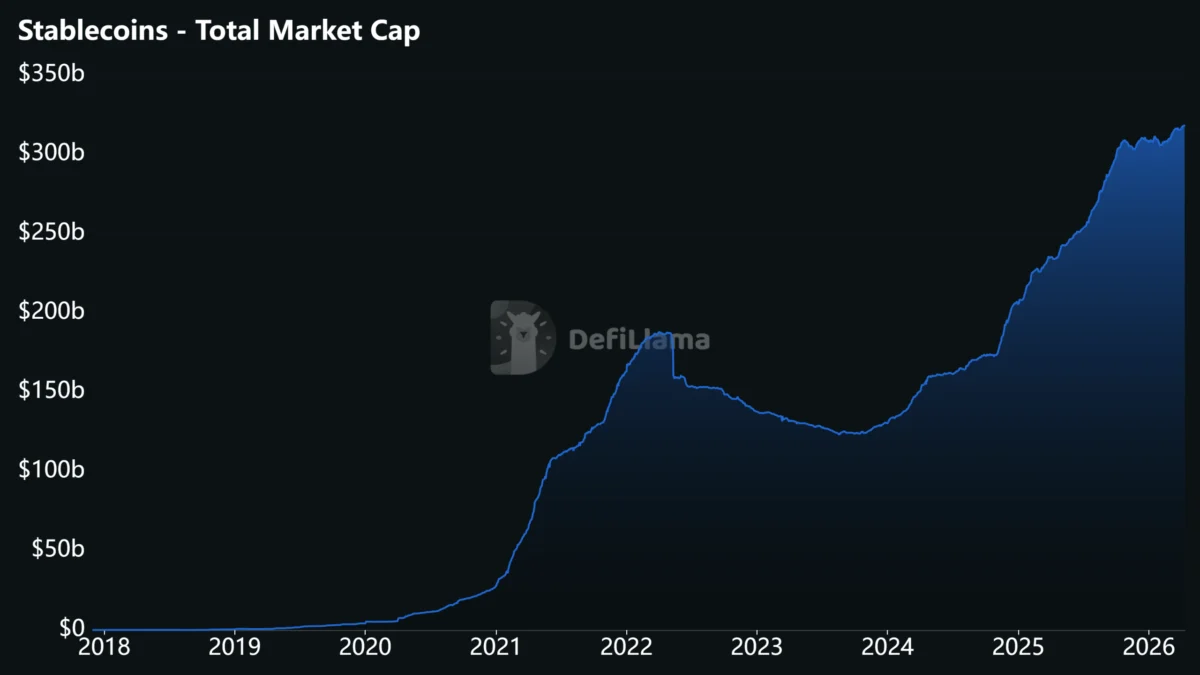
The 50% decline in stolen cryptocurrency is a landmark achievement for the industry, but it does not signal an end to the threat. Experts warn that the decline may be partially influenced by the "crypto winter" or bear market conditions that persisted through much of 2023. With lower Total Value Locked (TVL) in many DeFi protocols, the potential "prize" for hackers was smaller than it was during the 2022 bull market. As market valuations begin to recover and liquidity flows back into the ecosystem, the incentive for high-value hacks will inevitably rise.
The transition toward 2024 requires a sustained commitment to the "defense-in-depth" strategy. This includes not only technical code audits but also a focus on "human layer" security. As infrastructure attacks become the preferred method for hackers, companies must invest in employee training, phishing simulations, and more rigorous internal controls. The industry must also continue to foster an environment of information sharing, where details of exploits are disseminated quickly to allow other projects to shore up their defenses.
In conclusion, while the data from 2023 provides a reason for cautious optimism, the cryptocurrency security landscape remains dynamic and unpredictable. The emergence of new technologies, such as AI-driven social engineering or quantum computing threats, could quickly shift the advantage back to the attackers. As Ari Redbord noted, the key to maintaining this positive trend lies in vigilance and adaptability. By staying ahead of the curve and continuing to collaborate with global law enforcement, the cryptocurrency industry can build a more resilient infrastructure that fosters greater trust among institutional investors and the general public alike. The halving of stolen funds is not a victory, but a successful defensive stand in a war that is far from over.