The global cryptocurrency ecosystem faced its most turbulent year on record in 2025, with cybercriminals and state-sponsored hacking groups siphoning an unprecedented $2.7 billion from exchanges, decentralized finance (DeFi) protocols, and individual wallets. According to comprehensive data released by leading blockchain forensics firms, including Chainalysis, TRM Labs, and De.Fi, the total losses represent a significant escalation in both the sophistication and scale of digital asset heists. This figure surpasses the $2.2 billion stolen in 2024 and the $2 billion recorded in 2023, signaling a persistent and growing threat to the integrity of the burgeoning Web3 economy.
The year was defined by a series of high-profile breaches that targeted the very infrastructure of the crypto market. While dozens of platforms were compromised throughout the twelve-month period, a single massive heist against the Dubai-based exchange Bybit accounted for more than half of the year’s total losses. This incident, along with several others, has reignited intense scrutiny regarding the security protocols of centralized exchanges and the vulnerabilities inherent in decentralized smart contracts.
The Bybit Breach: A Historic Financial Heist
In February 2025, the cryptocurrency world was shaken by the announcement that Bybit, one of the world’s largest and most liquid digital asset exchanges, had suffered a catastrophic security failure. Hackers managed to infiltrate the platform’s internal systems, eventually gaining access to hot wallets and draining approximately $1.4 billion in various cryptocurrencies. The scale of the Bybit hack is difficult to overstate; it stands as the largest single cryptocurrency theft in history and ranks among the most significant financial robberies in human history, rivaling the physical theft of central bank reserves.
The investigation into the Bybit incident saw immediate collaboration between private cybersecurity firms and international law enforcement agencies. Within weeks, the Federal Bureau of Investigation (FBI) joined blockchain analysts in attributing the attack to the Lazarus Group, a notorious cyber-warfare unit operating on behalf of the North Korean government. The attribution was based on distinct "on-chain" signatures, including the specific methods used to obfuscate the movement of funds and the utilization of known North Korean-linked mixing services.
Before the Bybit catastrophe, the benchmarks for massive crypto heists were the 2022 attacks on the Ronin Network and the Poly Network. The Ronin Network breach, which targeted the infrastructure supporting the popular play-to-earn game Axie Infinity, resulted in the loss of $624 million. Similarly, the Poly Network exploit saw $611 million stolen, though a significant portion of those funds was eventually returned by the hacker. The Bybit heist of 2025 more than doubled these previous records, highlighting a shift toward targeting high-capacity centralized entities with massive liquidity.
The Role of North Korea in Global Crypto Instability
The 2025 data reinforces a grim reality for the digital asset industry: the Democratic People’s Republic of Korea (DPRK) has become the most prolific and successful predator in the crypto space. Chainalysis and Elliptic reported that North Korean state-sponsored hackers were responsible for at least $2 billion of the $2.7 billion stolen during the year. This represents nearly 75% of the total value lost to cybercrime in the sector for 2025.
Since 2017, it is estimated that Kim Jong Un’s regime has successfully stolen approximately $6 billion in digital assets. For the DPRK, these heists are not merely criminal enterprises but a critical component of national strategy. International observers and UN sanctions monitors have long argued that these stolen funds are directly funneled into the North Korean government’s prohibited nuclear weapons and ballistic missile programs. By bypassing traditional financial systems through the use of decentralized mixers and cross-chain bridges, North Korea has found a way to mitigate the impact of global economic sanctions.
The tactics employed by North Korean actors have evolved significantly. While early efforts focused on simple phishing and social engineering, the 2025 campaigns showed a high degree of technical prowess, including the exploitation of zero-day vulnerabilities in exchange software and the use of "poisoned" software updates to gain persistent access to administrative credentials.
Major Exploits in the DeFi and Protocol Sectors
While the Bybit heist dominated headlines, the decentralized finance (DeFi) sector remained a primary target for attackers due to the transparency of smart contract code, which allows hackers to hunt for bugs in public view. Several significant breaches occurred throughout the middle of the year, demonstrating that even established protocols remain vulnerable.
In May 2025, the decentralized exchange Cetus was hit by an exploit that resulted in the loss of $223 million. The attack targeted the liquidity pools of the platform, utilizing a flash loan-assisted manipulation that allowed the attacker to drain assets in a matter of minutes. This was followed by a sophisticated breach of Balancer, a prominent protocol built on the Ethereum blockchain. In the Balancer case, hackers exploited a subtle "rounding error" within the protocol’s accounting logic, a vulnerability that allowed them to slowly drain $128 million before the developers could deploy a fix.
Centralized platforms were not immune beyond the Bybit incident. Phemex, another major exchange, reported a security breach involving its hot wallet infrastructure. Cybercriminals managed to exfiltrate more than $73 million by compromising the private keys used to authorize outgoing transactions. These incidents collectively illustrate that no segment of the industry—whether centralized or decentralized—is currently "unhackable."
Analytical Breakdown of the 2025 Theft Data
The $2.7 billion total for 2025 was corroborated by multiple independent sources, each using different methodologies to track illicit flows. Chainalysis, which provides data to government agencies and financial institutions, noted that in addition to the major platform heists, they tracked approximately $700,000 stolen from individual private wallets through sophisticated phishing scams and "drainer" scripts. While this is a small fraction of the total, it represents a devastating loss for thousands of individual retail investors.
The REKT database, maintained by the Web3 security firm De.Fi, also confirmed the $2.7 billion figure. Their analysis suggested that while the number of individual "rug pulls" (scams where developers abandon a project and run with investor funds) had slightly decreased, the "exploit" category—where legitimate code is compromised—had surged in value.
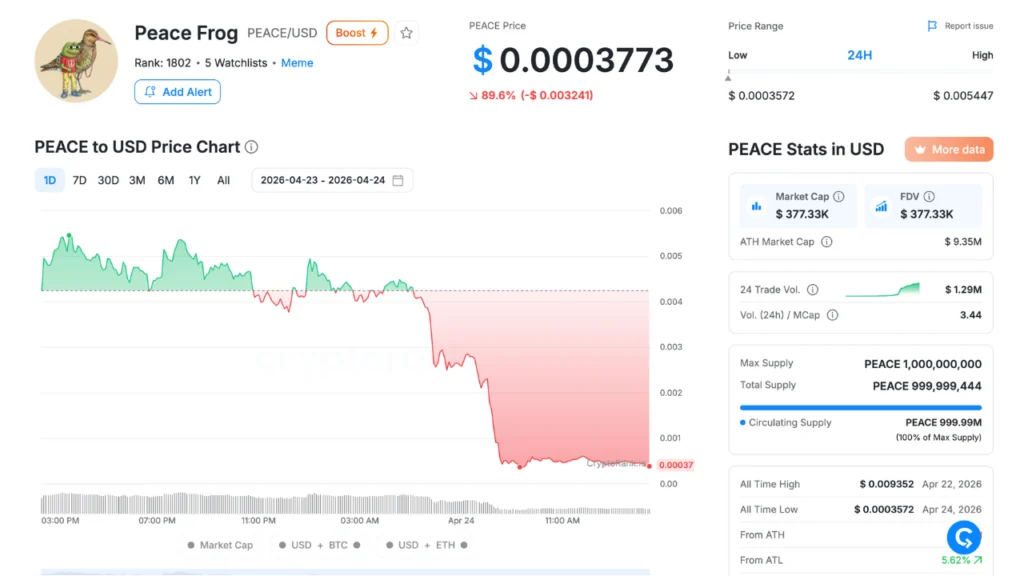
A comparison of the last three years reveals a concerning upward trend:
- 2023: $2.0 billion stolen
- 2024: $2.2 billion stolen
- 2025: $2.7 billion stolen
This 22% increase from 2024 to 2025 suggests that despite advancements in blockchain security and the emergence of more robust auditing firms, the offensive capabilities of cybercriminals are currently outpacing defensive measures.
Industry Responses and the Push for Regulation
The unprecedented losses of 2025 have triggered a wave of responses from industry leaders and regulators. Following the Bybit hack, several major exchanges announced the formation of a "Global Security Alliance" intended to share real-time threat intelligence and blacklist addresses associated with North Korean laundering activity. However, critics argue that such measures are often "too little, too late" once the assets have been moved through decentralized mixers.
Governments have also intensified their focus on the "off-ramps" of the crypto world. In the wake of the FBI’s report on the Bybit heist, the U.S. Treasury Department issued new guidance targeting over-the-counter (OTC) traders and smaller exchanges that may unknowingly facilitate the conversion of stolen crypto into fiat currency for North Korean agents. There is also renewed pressure on the developers of "privacy coins" and mixing protocols to implement "compliance-by-design" features, though this remains a point of heavy contention within the privacy-focused crypto community.
Security firms are advocating for a shift in how protocols are built. Rather than relying on a single audit before launch, many are now calling for "continuous auditing" and the implementation of "circuit breakers" that can automatically pause a protocol if suspicious outflow patterns are detected.
Broader Implications and the Future of Digital Assets
The record-breaking thefts of 2025 pose a fundamental challenge to the mainstream adoption of cryptocurrency. For digital assets to serve as a viable alternative to traditional finance, the industry must solve the "security gap" that currently makes it a playground for state-sponsored hackers and sophisticated criminal syndicates. The loss of $2.7 billion in a single year not only damages the financial standing of the affected platforms but also erodes the trust of institutional investors who are wary of the "wild west" nature of the market.
Furthermore, the geopolitical implications are profound. As long as cryptocurrency remains an effective tool for the DPRK to fund its military ambitions, digital assets will be viewed through the lens of national security rather than just financial innovation. This likely means that the coming years will bring even more stringent oversight, potentially altering the decentralized nature that originally defined the technology.
As 2025 draws to a close, the cryptocurrency industry finds itself at a crossroads. While the technology continues to evolve and attract billions in capital, the shadow of the $2.7 billion record hangs heavy over the market. The events of this year serve as a stark reminder that in the world of digital finance, code is not just law—it is also the primary frontline in a global, high-stakes conflict between innovation and exploitation.